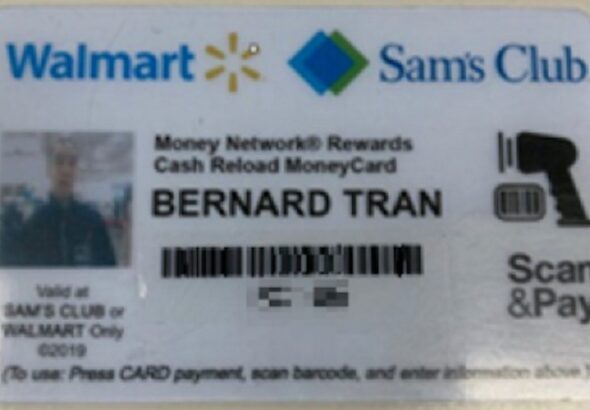
Cybercriminals exploit vulnerabilities in payment systems, compromising credit card details. Once obtained, this information is used for...
Of course, not all the popular and widely-used dark web sites and things like marketplaces on the...
Five or six times a day, a man from Texas injects a dose of carefully measured fentanyl....
Darknet is your best source for the latest hacking tools, hacker news, cyber security best practices, ethical...
Many vendors still sell fentanyl on mainstream dark web markets, disguised using names such as “China White”...
All that one can expect from a deep web marketplace when it comes to anonymity and security....
The DEA and other federal agencies have made a formal commitment to reducing the flow of fentanyl...
With the rise of social media apps, their convenience and lack of regulation, platforms including TikTok, Snapchat...
It’s incredibly common for darknet marketplaces to be held for ransom by hackers or attackers. These attacks...
These markets are dangerous anyway and shouldn’t be accessed even if they’ve onion addresses. One of the...