Still, according to investigations by the world’s best cybersecurity researchers and hackers, this shadow web is just a rumor. As you can notice if you read the list, many of the things for sale on the dark web are shams, designed to get your bitcoins without making good on the promise. Of course, if someone is actually looking to buy access to such things, they don’t earn a lot of sympathy as victims of the scam. However, the fact that in many cases the services advertised are just scams doesn’t make the dark web less dangerous or disgusting. The dark web is more than a distant threat hidden deep within the internet. As a couple of real-world examples show, it’s an active site for the preparation and monetization of cyber attacks.
There is no way to measure the exact terabyte amount, as much of this data hides behind secure servers. Countries differ in how aggressively they monitor Dark Web activity. In some authoritarian states, accessing Tor nodes can flag you for surveillance. Darknet is your best source for the latest hacking tools, hacker news, cyber security best practices, ethical hacking & pen-testing.
Types, Viewability, And Risks Of Deep Web Content
Going on the dark web has to be intentional since it requires a user to have specific tools to access it, such as the Tor browser and a Virtual Private Network (VPN). The shadow web is the next layer beneath the dark web and is said to be worse. A lot of its information is speculative and conflicting since there is tremendous secrecy surrounding it. The information available on message boards and forums suggests a paywall where users can see truly hardcore and shocking content. The shadow web is also believed to be the place where significant criminal networks and activities exist.
NordVPN is a high-performing VPN we frequently recommend to our readers, and 1Password is a secure password manager we have reviewed in detail. Both of these are excellent utilities you can try without second thoughts. There are many, but my personal favorite is ProtonVPN (free version available). If you’re still up for looking at the dark side of the internet for reasons best known to you, here are a “few” things to take note of. While the dark web is a part of the deep web, there are stark differences between those two.
Is The Dark Web Illegal?
The dark web is a hidden part of the internet where illicit activities thrive and anonymity is prioritized. As such, it is a breeding ground for various types of threats that can jeopardize both individuals and organisations. From cybercriminals and hackers to illegal marketplaces and scams, the dark web poses a wide range of dangers that users must be aware of in order to protect themselves and their sensitive information. Understanding the types of threats on the dark web is crucial for taking the necessary precautions to safeguard against potential harm. The dark web plays a critical role in cybersecurity because it serves as a hidden marketplace and communication hub for cybercriminals.
August’s Top VPN Discounts

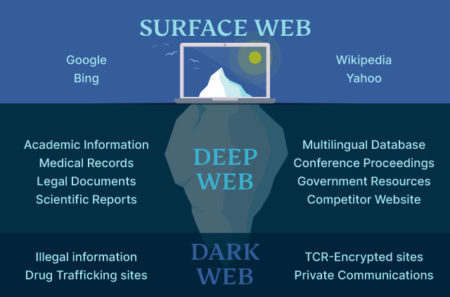
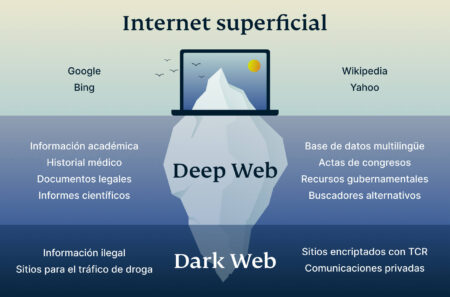
While it’s the most visible tip of the internet iceberg, it only represents a small fraction of all the content available on the internet. Whatever data you access, the organization holding onto that data has it as well. In comparison, the dark web operates on the principle of total anonymity and leaves everything in your hands. The deep web helps protect your private information, but is not in your hands.

Difference Between Deep Web And Dark Web
Dark web hosts project which ends with .onion (aka onion sites) and not .com, .net, .org, etc. that we generally operate with. And since normal browsers can’t browse such websites, you need something like the Tor browser to surf the dark web. In a nutshell, the deep web remains “open” to its respective owners and stays “closed” to others. And if someone tries to access the deep web without proper authorization, it would be termed as hacking, which is again illegal. Due to the anonymity of the seller and buyer, these marketplaces are full of fraudulent sellers. Ultimately, anybody can claim to have something for sale, receive payment, and then keep the money.
The dark web has more popular recognition than the deep web, especially in its association with illicit online activities and depiction on mainstream TV shows. It’s illegal to sell corporate data, for example, which seems to imply that the dark web would be the place to find the greatest treasure troves of maliciously obtained datasets. The dark web refers to any number of self-contained, encrypted overlay networks that live on top of the internet, inaccessible save for special tools and protocols, hence dark. The deep web is defined as the internet section that is not indexed by web crawlers.
Service Providers
Additionally, many Dark Web sites are discoverable only via special search engines, following links from one site to another, or word of mouth. The Deep Web is a section of the Internet that is inaccessible via search engines but can be accessed via normal browsers. It is composed of “non-indexed” content that is unreachable by the web crawlers used by Google, Bing, and other search engines to find and link pages.
BlackSuit Ransomware Sites Taken Down After Checkmate Operation
People use the surface web for mundane tasks like visiting their favorite website, watching movies online, or shopping. Technically speaking, the dark web is the content existing on darknets, closed-off networks that exist on top of the regular internet and use its infrastructure. The two terms are used interchangeably, just like the World Wide Web and internet are. However, unlike the clear net, the dark web is well hidden, can’t be accessed via a normal web browser, and is very likely illegal. Indexing is how search engines such as Google analyze and store data on websites, allowing them to appear when you search for them.
Roundup – Best VPNs For The Dark Web
However, these features can be used for both legitimate and malicious purposes. This is the primary reason why the US NRL developed the TOR technology used by most Dark Web visitors. Cybercriminals take advantage of the privacy and anonymity that the Dark Web provides for a variety of purposes. Dark Web marketplaces are used to buy and sell illegal goods and services. Forums hosted on the Dark Web host discussions on successful and ongoing cyberattacks, newly discovered vulnerabilities, and other details of cyberattacks. Dark Web users also use the platform to exchange tips and tools for performing different cyberattacks and fraudulent activities.
For accessing the Dark web, a VPN is essential for complete privacy. In this scenario, a VPN would be a great help to hide your internet activities. The sites visible to the Google search engine fall into the category of the surface web that anyone can access. The surface web is also known as indexed or visible web, which every user accesses in their daily internet activities.
Tor powers them using its protocol known as Tor Hidden Service Protocol. And the websites limited to the Tor network have a special .onion address. The dark web is home to the internet’s hidden sites, services, and products — some innocent, others downright dangerous.
- Downloading files from this environment can potentially expose your devices to a variety of threats and malicious content.
- Otherwise, I’d be in trouble since the Google Docs page on which I’m writing this article is part of the deep web.
- Expanding their reach – through the use of Dark Web monitoring tools – can be invaluable to a corporate cybersecurity and risk management program.
- Being unindexed does not necessarily imply that it is hidden; it simply means it is kept differently from the surface, indexed content.
- One of the most often transactioned goods on the dark web marketplaces is your data.
Therefore, to avoid trouble, make sure that you visit just reputable sites, apply secure connections, and adhere to a privacy directive. Possibilities of exposure to dangers like leakage of data or content violating the law are reduced, providing that the applicable users have the correct credentials and authorization. The Deep Web consists of countless legitimate applications, such as research or retrieval of personal medical records, or corporate management of data. Researchers generally use databases like JSTOR for articles, while healthcare providers maintain private information regarding patients in secure systems.
These are used to share and exchange information without public exposure. It consists of dynamic content generated by websites that require user interaction through forms or log-in just for proper viewing. Thus, the deep web is a significant part of various disciplines containing sensitive information that helps with academic and professional activities. It consists of private, secure, often password-protected, content requiring credentials or special access. Most activities on the deep web are legal and intended to protect user privacy. Most deep web websites require login credentials, often with two-factor authentication, and use encryption to protect user information and keep transactions private.



