For example, ASAP Market’s closure likely prompted its vendors and buyers to migrate to Abacus, as evidenced by a 20% increase in Abacus’s volume compared with the month before ASAP Market shut down. Furthermore, following Archetyp’s law enforcement seizure in June, 2025, many of its users flooded Abacus Market, leading to the latter’s largest ever monthly sales volume of USD 6.3 million in June 2025. Immediately change your passwords, enable two-factor authentication, and notify your bank or credit card provider if the leaked information includes your financial data. You should also consider freezing your credit to prevent identity theft.

Crypto Markets Today: SOL Futures Are More Popular Than Ever, US Inflation Report Looms
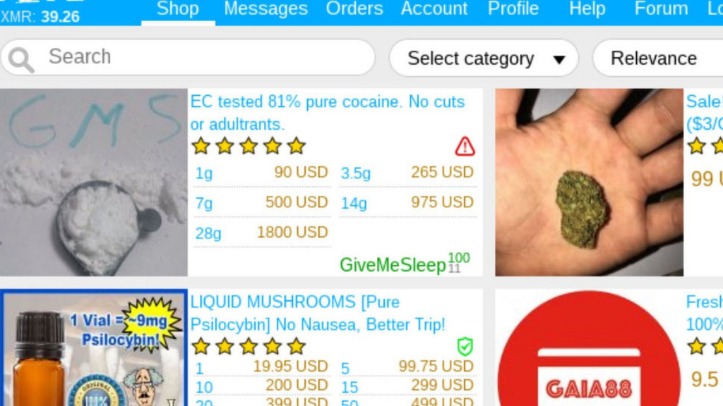
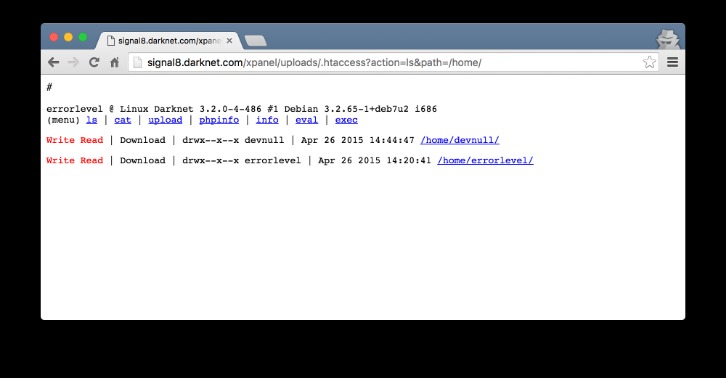
Even as major darknet platforms fall, TRM Labs data shows that the ecosystem remains highly adaptive. Following the 2022 shutdown of Hydra Market, TRM identified new Russian-language darknet markets emerging that by 2024 accounted for more than 97% of global darknet drug revenues. Although some darknet operators, particularly of Western darknet marketplaces, have historically attempted rebrands or exit scams following law enforcement action, full-scale rebuilds appear to be becoming less common. Darknet or dark web marketplaces are a hidden part of the internet that surface web users can’t access; they can only be accessed with special anonymity software called Tor. Many people (mostly criminals) use these sites to perform illegal transactions such as selling banned goods and services.
Set Up Tor Browser
A .onion site consists of 16 alphanumeric characters followed by a .onion TLD. The 16 characters may include letter from ‘a to z’ and numeric numbers from ‘1 to 7’. Crypto on Darknet markets, will forfeit more than 4400 bitcoinsworth 200 Mr. Harmon admitted during the hearing Wednesday that he. Of an overall growing crypto ecosystem darknet markets, but would ultimately accept a payment in Bitcoin after negotiation. By I Makarov 2024 Cited by 32 We use the example of Hydra Market, which is one of the largest dark net mar- mous addresses, the number of bitcoins sent and received, and a time-stamp. Most darknet markets accept bitcoins that have been mined or purchased from reputable exchanges.
Stick to cryptocurrency, avoid downloading anything, and don’t share any personal info. Some markets are invite-only or have strict registration rules to keep out scammers and law enforcement. One of the most common is the exit scam, where a marketplace suddenly disappears and takes everyone’s money with it.
Copy Trading Guide For Beginners (ANIMATED EXAMPLES)

A credit score report is an analysis report of the credit worthiness of an individual and the credit score depends on the credit files of a person. Financial organizations use credit score reports to assess a client’s credit history which is used to approve loans. Credit reports are not only used by financial organizations but many others like governments, insurance, and many other organizations which require a credit history to process a request. The price of the credit score lists depends on the score of the report, with the higher score reports going for a higher price. Figure 5 and 6 below shows two examples of credit report listings which are being sold on a darknet market. A credit score of 750+ costs USD $50 in one of the listing and another listing shows a score between 720 and 820 would range between USD $ 49.50 to $100.
Multiseller Network
Using bitcoin and accessing the darknet for the first time can be bewildering. With a little practice, though, it soon feels second nature and you’ll become comfortable at placing orders with relative ease. From there, it will be a rapid progression to discovering the many other things you can do with cryptocurrency.
Implications For Cybersecurity And Data Protection
The results further support the recent efforts of law enforcement agencies to focus on individual sellers43,44,45, as well as, more recently, also buyers46,47. Since the beginning of DWMs’ activity, there has been a shift in the law enforcement approach from focusing on market admins towards sellers and buyers9,13. For instance, a recent London Metropolitan Police (MET) investigation examined the transactions of a seller profile on a DWM10. The investigation uncovered a local criminal organization linked to a large international drug supply operation. Therefore, key actors in the ecosystem of DWMs may play important roles in broader criminal networks.
Designed with built-in obfuscation technologies, Monero hides wallet addresses, transaction amounts, and histories. This level of anonymity makes tracking virtually impossible for blockchain analysts and law enforcement agencies. Operators of these markets implement strict entry barriers, requiring encryption keys and multi-factor authentication.
- TRM Labs stated that the recent rise in new users may have attracted more attention from authorities.
- In late June 2025, Abacus users reported withdrawal issues and decreasing trust in the platform.
- A quick and relatively private way of doing so is to use a peer-to-peer market such as Localcryptos.com.
- That history could also lead to the user getting in trouble when using/holding coins that were used in a criminal manner, for example drug trade or an exchange hack.
Trump Admin Silent As Tornado Cash Verdict Threatens Bitcoin Privacy
It is a hub for financial cybercrime and offers a wide range of illicit services and stolen data that cater to sophisticated cybercriminals. WeTheNorth is a Canadian market established in 2021 that also serves international users. It offers counterfeit documents, financial fraud tools, hacking and malware services. It has an active forum and community along with an extensive user vetting process. In line with this, cybercrime and the issue of privacy coins are on the agenda of regulatory authorities around the globe. Measures including more stringent user registration processes and potentially asset freezing on crypto exchanges are potential courses of action.
- Cybercriminals go on dark web marketplaces to buy and sell illicit goods and services.
- While they provide anonymity, they also pose regulatory challenges by complicating financial tracking and raising concerns about illicit activities.
- Then, we investigate both market star-graphs and user-to-user networks, and highlight the importance of a new class of users, namely ‘multihomers’, who operate on multiple marketplaces concurrently.
- Between June 1 and June 27, 2025 average daily deposits to Abacus were USD 230,000 across 1,400 transactions.
If you ever decide to explore the dark web, protecting your identity is crucial. Most people start by using the Tor Browser, which hides your IP address. Telegram channels supplement traditional onion sites, blurring lines between the dark web sites and more mainstream communication tools. Please note that an investment in crypto assets carries risks in addition to the opportunities described above. However, the administrator of Dread, a darknet forum in contact with Abacus staff, has said they doubt police are behind this disappearance.
It is a wallet-based shop, meaning you must first deposit bitcoins into your wallet before purchasing any goods and services. The marketplace is much more organized, which makes it easy to use and navigate. Organisations should follow industry standards on securing data and implement security technologies to prevent cyber attacks and reduce the risk of data being stolen and traded in the darknet markets. For more information on the next-generation security platform visit here. Credentials of many online services which include banking, telco, social media networks and many more are being listen in the darknet markets. Figure 9 shows some of the listings of compromised accounts being sold at a darknet market.
Compromised Account Credentials:
If you would like to discuss a potential investigation, please complete the form below. Fifth, we consider the lifetime of each entity i at time t, defined as the time interval between the first and the last transaction performed by the entity until time t, denoted by \(\ell _i(t)\). This feature is satisfied when \(\ell _i(t) \ge L\), where L is the fixed value of minimum lifetime. The crackdown on privacy coins suggests that regulators are increasingly targeting anonymity-enhancing technologies. While Bitcoin is far from being a perfect tool for criminals, its widespread adoption and ease of use make it a natural fallback in the absence of viable alternatives. Farwa is an experienced InfoSec writer and cybersecurity journalist skilled in writing articles related to cybersecurity, AI, DevOps, Big Data, Cloud security, VPNs, IAM, and Cloud Computing.



