The same general process applies to other operating systems, as Tor is also available for Mac and Linux. By keeping an eye on these alternative platforms and trends, you gain a deeper understanding of how privacy, anonymity, and underground markets adapt to new technologies and challenges. As digital ecosystems morph, staying informed and agile will help you make the most of evolving privacy tools—or avoid stepping into ever-more complex traps. These domain names are not registered with a central authority but are instead derived from cryptographic keys. Impreza Hosting is a service that helps you host a site on the Tor network.
What Is The Darknet?
You can read our NordVPN review for more information, or try it out yourself using the 30-day money-back guarantee. Valentina Bravo is an editor at Cloudwards with a rich background in technology topics, particularly productivity tools and online security. She holds a Bachelor’s degree in Liberal Arts and a triple Master’s degree in Literary and Cultural Studies. Outside of work, she is a travel enthusiast, music lover and avid learner interested in global cultures, spirituality, psychology and neuroscience. The dark web is a controversial part of the internet, famous for being a hotbed for illegal and criminal activity. Read our comprehensive “what is the dark web” guide to understand how it works and the risks and benefits.

Can You Be Traced On Tor?

Upon opening the Tor website, you will be presented with various download options for the operating systems that Tor supports, including Windows, macOS, Linux, and Android. As stated above, we don’t condone any activity—on the dark net or otherwise—that is forbidden by law. With the above dangers, it’s imperative to tread carefully as you step into the dark web. Following the NYT, the BBC launched a dark web “mirror” of their international edition in 2019. Note that some features of the normal website are not available on the .onion version, including BBC iPlayer. For totally hiding all of your online antics, you’ll want to also use a VPN.
Protect Yourself Against Tracking, Surveillance, And Censorship

This may be useful in countries that block Facebook, for example. If you need a way to organize as an activist or you want to discuss censored topics with others, my first suggestion is to stick to offline meetups. The second, less secure option is to use encrypted messaging apps with ties to specific non-profit or activist organizations. For example, Briar is an extremely private chat app designed to help journalists communicate anonymously with sources. Signal is our Editors’ Choice for private messaging apps because it does a great job of blending privacy and social media functionality for a highly customizable chat experience. The top layer is referred to as the clear or “surface web,” which is what you’re accessing while reading this article.
More On Tor Onions
Tor protects your identity inside its network, but it doesn’t hide everything. Your ISP still knows you’re using Tor, and entry nodes can see your real IP address. A VPN adds protection before Tor, closing these gaps without breaking access to .onion sites.
It is also used to facilitate human trafficking, money laundering, and worse. The dark web is a refuge for information leakers and whistleblowers. The dark web is the perfect avenue for communicating and publishing sensitive information with no fear of retribution, such as imprisonment.
Social Media
With NordVPN, click on the “shield” icon to activate Threat Protection Pro. It will provide you with extra protection by blocking malware, trackers and harmful ads as you browse the deep web. It’s estimated that the deep web makes up between 90% and 95% of the entire internet.
How To Get On The Dark Web In 2025: A Step-by-Step Guide
The darknet is a part of the internet that is not indexed by conventional search engines, often requiring specific software and configurations to access. It is a place where anonymity and privacy are highly valued, making it a frequent point of interest for researchers, privacy advocates, and individuals concerned about online security. If you want to be extra safe, routing your connection through a VPN and then accessing the dark web using the Tor browser provides more security than Tor alone. You can also use the Tails operating system to further protect yourself. If you’re just browsing the dark web out of curiosity, Tor, or a Tor and VPN configuration is safe enough. If you’re trying to hide from an oppressive government or want to be a whistle-blower for something illegal, take as many steps as you can to be safe.
For example, one of the most common ways to access both the deep web and the dark web is through Tor. In order to properly understand how the deep web works, you first have to understand a few fundamentals of how the regular internet operates, especially as it relates to search engines. Websites that exist purely on the deep web have different access, so there’s a level of privacy for the website hosts that isn’t possible on the regular internet. If your website is only accessible through the deep net, tracking down the physical location of your servers is much harder than it would be for a regular website. Aleksander Hougen, the co-chief editor at Cloudwards, is a seasoned expert in cloud storage, digital security and VPNs, with an educational background in software engineering.
Such sites include blogs, gaming sites, social media, and super-encrypted email platforms. Fortunately, it’s not a criminal offense if you simply search the dark web, but if you use it to carry out illegal activities, you get in trouble. Information on the dark web is not meant for public consumption, and the dark web protects personal data intended to be private. To further obscure transactions, Bitcoin users can employ digital currency exchanger services to convert their Bitcoin into online game currency, which can later be converted back into fiat currency. Services such as Tumblers are also available on the dark web to help hide transactions. However, Bitcoin’s relevance in the digital world has also made it a scam target.
- As such, the dark web has attracted many parties who would otherwise be endangered by revealing their identities online.
- While some threats on the dark web are well-known, others may use its notorious reputation to trick users into paying large sums of money.
- There are also many tools that can be use to monitor the dark web and scan for personally identifiable information and even respond to attacks.
- We may earn a commission when you buy through links on our sites.©2025 GIZMODO USA LLC.
- With all this data, your ISP could create a very accurate profile of you and link it to your IP address.
- It’s divided into commercial links (from crypto services to gambling sites) and non-commercial links (like social media).
- As a result, you can be exposed to different malware types, including botnets, ransomware, keyloggers, and phishing.
- A single misstep, like skipping a leak test or using the wrong browser, can undo all your privacy efforts.
- If one tries to visit the dark web with a regular browser, there will be no web pages to visit.
- For example, Facebook maintains an official Tor hidden services address at “facebookwkhpilnemxj7asaniu7vnjjbiltxjqhye3mhbshg7kx5tfyd.onion”.
- DefCon, ProPublica, the CIA, various libraries, and open-source software providers also feature in this area of the internet.
I also report on online scams and offer advice to families and individuals about staying safe on the internet. Before joining PCMag, I wrote about tech and video games for CNN, Fanbyte, Mashable, The New York Times, and TechRadar. I also worked at CNN International, where I did field producing and reporting on sports that are popular with worldwide audiences. These tools, designed for legitimate purposes, serve functions such as protecting user IP addresses and providing a proxy network for journalists reporting from precarious territories.
As you are now familiar with the three different sections within the entire world wide web, let’s take a closer look at how you can access the dark web anonymously. We’ve also previously mentioned the “dark users” that use the dark web for illegal reasons, but the less said about them, the better. Absolutely no one knows who’s surfing on the dark web, who is selling, who is buying or anything like that – as long as you take the correct safety and online privacy precautions. The dark web is infamous for containing sites such as Silk Road and other marketplaces where users could potentially buy drugs and/or weapons, stolen credit cards, IDs, and much more. The majority of the web is called the “deep web” (often referred to as the “invisible” or “hidden” web).
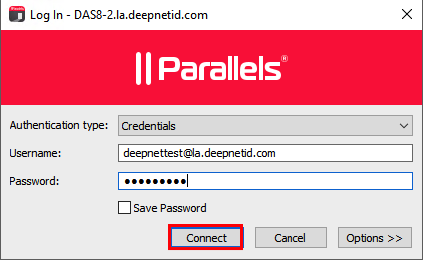
Step-by-Step Guide: How To Access The Dark Web Using Tor Browser
Deep web sites may be concealed behind passwords or other security walls, while others simply tell search engines to not “crawl” them. Without visible links, these pages are more hidden for various reasons. All commonly public-facing websites accessed via traditional browsers like Google Chrome, Internet Explorer, and Firefox are contained here. Websites are usually labeled with registry operators like “.com” and “.org” and can be easily located with popular search engines. Law enforcement officials can exploit that weakness using “Tor-exit-node” monitoring techniques to expose users’ IP addresses and potentially trace activity back to the original users.

Indeed, Facebook, The New York Times and now even the CIA have sites on the dark web, hosting “onion” versions of their pages that can be accessed via the Tor browser. The spy agency is hoping to securely and anonymously collect tips, though its entire website, including job listings, are available on the onion service. It’s a lifeline for activists, whistleblowers and journalists seeking safe spaces to connect and speak freely. Social platforms buzz with anonymous conversations, even as law enforcement hunts through digital shadows to crack down on criminal rings.
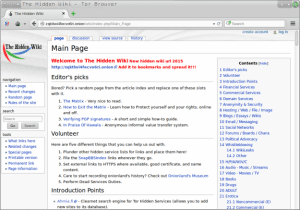
Your traffic is relayed and encrypted three times as it passes over the Tor network. The network is comprised of thousands of volunteer-run servers known as Tor relays. The Hidden Wiki is a popular onion link directory on the dark web offering categorized lists of sites. Check onion links through trusted directories, user reviews, and reputation checks. Use directories like The Hidden Wiki or Dark.fail, which list verified and regularly updated onion links. Install Tor Browser from the official website, adjust security settings to “Safer” or “Safest,” and only use trusted onion links from verified directories.