
They use pseudonymous wallets, privacy coins (like Monero), mixers, chain-hopping, and non-KYC platforms to obscure transaction trails. There’s also a privacy angle—some users live in countries with censorship or surveillance, and the dark web gives them a space to communicate or access information more freely. The second category consists of data stores, which specialize in stolen information.
Using Tracker Apps To Monitor Your Card Data
Strong passwords and security tools add extra layers of defense against cyber threats. These sites are hard to find and use special software to stay secret. You can also limit your risk by being picky about your ATMs, where criminals sometimes install card skimming devices. These are hard to detect, but only using ATM machines inside banks or other physical buildings offers some protection, Thomas says. As with credit cards, the location of the victim whose information is up for sale has a significant influence on price.
How Flare Can Help With Dark Web Monitoring
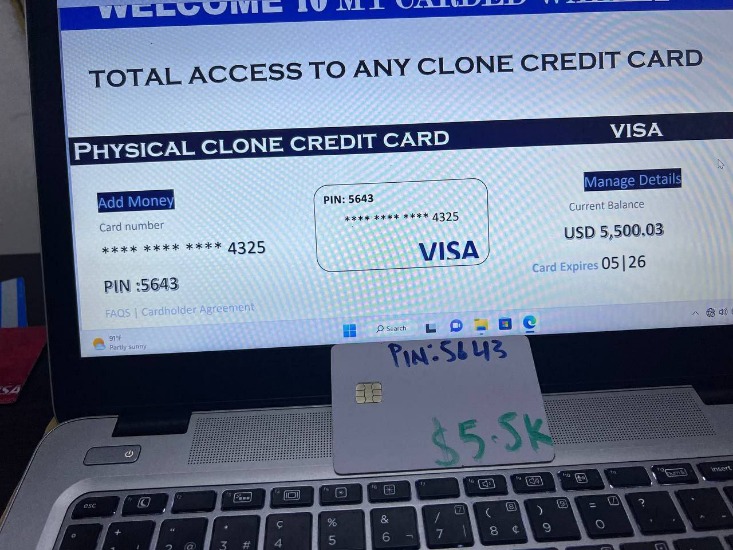
Instead of card numbers and CVVs, criminals steal usernames and passwords that they’ve gathered either through phishing or malware. They can then sell the account credentials to a buyer who can log in and drains the funds, or the vendor can transfer the requested amount of money from the victim’s account to the buyer’s account. Credit cards can be sold as physical or digital items on the dark web. Credit card details used for online fraud are cheaper and can be sent in a text message. Physical cards are usually cloned from details stolen online, but can be used to withdraw from ATMs. Because the merchant requires equipment to clone the card and must send the buyer a physical product complete with PIN number, the price for cloned cards is much higher.
Access Websites Safely
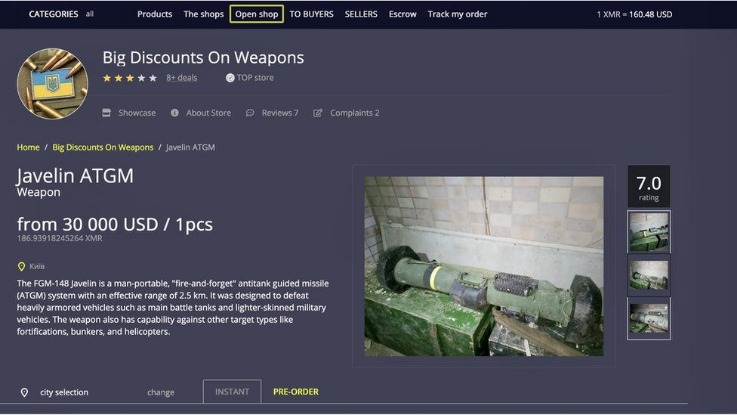
- The most common activities are the unlawful transfer of drugs, explicit data, firearm deals, and dark web credit card fraud.
- Japan, the UAE, and Europe have the most expensive identities at an average of $25.
- If you can, use an online wallet like Apple Pay or Google Pay, says Pascal Busnel, a director with ACA Group, a provider of risk, compliance and cyber solutions.
- The Dark Web operates as a shadow marketplace, with prices for stolen data influenced by the interplay of database security vulnerabilities, demand, and risk.
- Credit cards, Paypal accounts, and fullz are the most popular types of stolen information traded on the dark web, but they’re far from the only data worth stealing.
- Join us as we break down and discover the methodologies of card fraud using our dark web monitoring tool, Lunar.
This proactive monitoring enables businesses to track and investigate potential threats in real-time, helping to prevent fraud before it can impact their operations. The use of such platforms is crucial for maintaining the integrity and security of customer data, and it provides an additional layer of defense against cybercriminal activities. Comparitech researchers gathered listings for stolen credit cards, PayPal accounts, and other illicit goods and services on 13 dark web marketplaces. For legal reasons, we will not publicly disclose which marketplaces were used. Information in the listings was entered into a spreadsheet for data analysis and statistical calculations. In addition to just selling credit card details, some threat actors offer a “complete package” often referred to as “Fullz”.
Classic darknet markets sell diverse illegal goods; data stores focus on leaked or stolen data like credentials, databases, and ID records. By supplying stolen data, these dark web links fuel many online scams and identity theft operations, playing a critical role in the darker aspects of the internet. When Torrez closed in December it was one of the largest English-language marketplaces in the world selling drugs, hacking tools, counterfeit cash and criminal services.
Top Cybersecurity Discord Servers To Join
Many of the stolen card numbers were hacked using a tactic cybersecurity experts call “brute-forcing,” the report said. In brute-forcing, a computer tries to guess your password, testing a series of numbers until it gets it right, possibly in as few as six seconds. A computer is able to “make thousands of guesses a second,” Briedis said. “After all, criminals don’t target specific individuals or specific cards. It’s all about guessing any viable card details that work to sell.” It is understood that the data included such highly sensitive information as the primary account number of the credit cards concerned, along with expiration dates and the card verification value, CVV2, security code. But that’s not all; there are also cardholder details such as their full name, address, date of birth and telephone number as well as email address.

The stolen credit card data is typically offered in a shopping cart format, where the “buyer” can check off which credit cards they want to purchase based on a menu of available credentials. It has built a reputation for being a reliable source of stolen credit card data and PII. Renowned for its extensive inventory of financial data and sophisticated operating methods, Brian’s Club is a key player in the underground economy of financial cybercrime. “The dumps also include magnetic stripe data, allowing criminals to create physical card clones,” Draghetti warned. One of the most recent and devastating cyberthreats facing merchants is the rise of Magecart hackers, according to Mador. These groups of cybercriminals have been very active in the past two years, stealing credit card data by injecting malicious code into the checkout pages of merchants’ e-commerce stores.
Million Stolen Credit Cards Given Away Free On Dark Web
By regularly checking your credit reports and statements, you can quickly identify any unauthorized charges or suspicious activity. Look out for unfamiliar transactions or sudden changes in your credit score. If you notice anything unusual, contact your credit card company immediately to report the issue.
How To Prevent Getting Your Credit Card Stolen
Opt for reputable and trusted payment gateways that offer strong encryption and advanced security measures. These platforms often provide additional layers of authentication, such as two-factor authentication or biometric verification, ensuring the protection of your financial information. For example, hackers may sell credit card information in bulk, allowing others to commit fraud and financial theft. Dark web transactions play a key role in fund transfers for credit card fraud. Cybercriminals use cryptocurrency to buy and sell stolen card data anonymously.
Tools And Services For Detection
To minimize the risk of payment data exposure, only shop from reputable retailers, use digital payment methods or one-time private cards, and protect your accounts with two-factor authentication. Using PureVPN can create a private and secure connection to the internet and reduce the risk of getting your stolen set of dark web credit cards. This software encrypts the traffic before routing it to a remote server. More than being a place for the secure transmission of information and communication, the dark web has become the breeding ground for illegal activities. The most common activities are the unlawful transfer of drugs, explicit data, firearm deals, and dark web credit card fraud. Hundreds of millions of payment card details have been stolen from online retailers, banks and payment companies before being sold on online marketplaces such as UniCC.
For police, who would prefer criminals to face justice, this kind of exit causes mixed feelings. The darknet is a part of the internet only accessible through special browsing software. This page may contain sensitive or adult content that’s not for everyone. To view it, please log in to confirm your age.By continuing, you also agree that use of this site constitutes acceptance of Reddit’s User Agreement and acknowledgement of our Privacy Policy. Now that I have, I don’t really know what to do and im kinda bored.
Learn how to automate financial risk reports using AI and news data with this guide for product managers, featuring tools from Webz.io and OpenAI. Established in 2022, WizardShop is one of the biggest data stores on the dark web, focusing mainly on carding and financial data. Its focus on financial fraud and high-value transactions has attracted a dedicated user base, contributing to its growing reputation and market value. To expand their reach, some marketplaces established parallel channels on Telegram. This further complicates monitoring efforts because now you need to search for the related Telegram channels and track activity there and on the marketplace itself. Contrary to popular belief, most carding platforms no longer hide in the dark web (i.e. the Tor network).



