Examples include software as a service (SaaS) solutions, paid news websites, and streaming services. Unlike the Dark Web, sites on the Deep Web can be accessed using normal web browsers like Firefox, Google Chrome, and Safari. Also, these sites are often linked to publicly accessible pages, making them findable and accessible by users with the right login credentials and willingness to pay. For example, sites like Netflix are reachable from search engines, but the videos hosted on the site are only accessible to users who have created an account and paid a subscription fee. The Deep Web is the portion of the Internet not indexed by traditional search engines. It often requires a login (such as a username and password) or special software to access.
What Are Some Examples Of Deep Web Websites?
Within this domain, another layer called the Dark Web exists, shrouded in secrecy and often misunderstood. Accessing the deep web, which encompasses a vast array of unindexed resources, does not require specialized tools. However, its architecture poses unique challenges, particularly in locating specific information.
- This makes it even harder for third parties to see your email traffic.
- When it comes to dark web safety, the deep web dangers are very different from dark web dangers.
- Though it’s still helpful, a static list isn’t enough (we try to keep our own, the one above, up-to-date, though).
- Some of the deep web sites do not use standard top-level domains (TLD) such as .gov, .com, .net, etc.
- Before we unpack the dark web’s threats, let’s explore how and why users access these sites.
- Websites that exist purely on the deep web have different access, so there’s a level of privacy for the website hosts that isn’t possible on the regular internet.
Dark Web Tools And Services
Some other uncommon search engines include Startpage, Brave Search, and Ecosia. It certainly isn’t illegal – not when it is actively used by all websites and permeates everything we do online, apart from idle browsing. The Deep Web is crucial for ensuring privacy, security, and the efficient operation of various systems, including government databases, academic research platforms, and business intranets.
Your online activity and communications remain private and secret on the dark web. Because of this, some people use it to get around government restrictions, while others use it for illegal activities like smuggling drugs and weapons. With rising online privacy concerns in the current digital age, the Tor network’s anonymity is becoming essential. It is a good way to prevent third parties from tracking online activities.
What To Do If You See Something Illegal
So yes, the onion network and the deep web are both legal, it’s only the dark web which is illegal and may cause problems for you. You also need to know that more than half the sites and sellers on the Dark web can’t be trusted, and are just scammers. That’s so because it’s already an illegal arena, so you can’t exactly go to the authorities about it. Basically, any site with .onion extension is a site on the Tor network, and can be easily accessed with a Tor browser, although the site may or may not be illegal.
Onion Links: How To Access Them
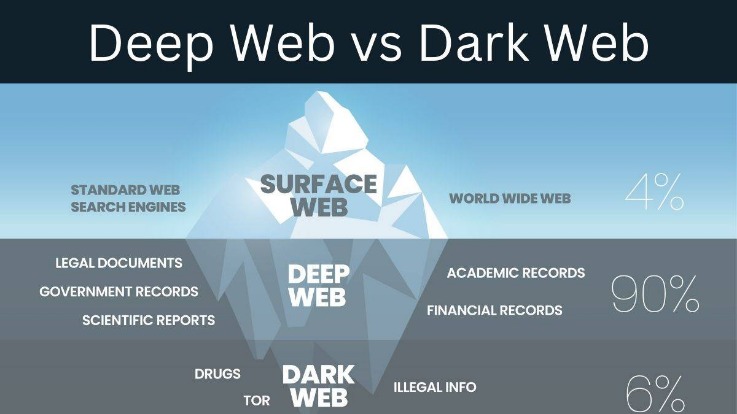
However, it is essential to practice safe browsing habits to avoid all that information you’ve been accessing on the deep web ending up on one of the dark web’s marketplaces. Use strong passwords, a reliable VPN, and think twice before logging into your banking account via a public Wi-Fi connection. Another thing hidden from the public eye on the deep web is private databases. This exposure can lead to legal repercussions if law enforcement tracks illegal activities back to you, despite the anonymity. The Deep Web makes up the majority of the internet, far surpassing the size of the Surface Web, which includes all publicly accessible websites. Intranets, or internal networks used by companies and academic institutions, cannot be accessed by the public.
At the same time, the primary job of a smart search engine is not to simply find information. What you really want it to do is find the most relevant information. Otherwise, you’re left awash in a sea of cluttered data that leaves you wishing you had never clicked on that search button. For citizens living in countries with violent or oppressive leaders, the dark Web offers a more secure way to communicate with like-minded individuals. If you haven’t heard of Bitcoin, it’s basically an encrypted digital currency. Like regular cash, Bitcoin is good for transactions of all kinds, and notably, it also allows for anonymity; no one can trace a purchase, illegal or otherwise.
He also leads the video production team and helps craft e-courses on online technology topics. Outside of the professional realm, he is a digital nomad with a passion for traveling, having lived in many countries across four continents. The greatest difference between them is that while you can still access the deep web with regular browsers, web pages on the dark web run on overlay networks. VPNs keep you safe in other ways, including preventing IP address leaks and using confirmed no logs that clear your online and browsing data. High-quality VPNs now feature obscure servers for stealth operations and superfast and secure protocols like OpenVPN and WireGuard.

Understanding The Surface Web: Your Guide To The Visible Internet
It uses 256-bit AES encryption for maximum data protection, has a no-logs policy, and protects against IPv6, DNS, and WebRTC leaks. It prevents your IP address from ever falling into the wrong hands in the depths of the internet via “Network Lock,” its kill switch available across all major platforms. An exceptional VPN service with high-speed servers and robust security features. It enables safely accessing any website on the deep web, allowing users to browse their favorite content without restrictions. Already a household name in the VPN market, its developers keep upgrading it with new features to keep it ahead of its competitors. One of the most trusted VPNs for the deep web and the dark web security, it effectively blocks malware, ads, web trackers, and other online threats.
- This type of government surveillance applies mostly to countries with environments that are hostile to free speech.
- The Deep Web raises important questions about privacy, security, and ethics.
- A VPN is a “Virtual Private Network”, it may sound complicated but it’s just a software which hides your actual IP address, and assigns you a secondary IP which can’t be linked back to you.
- Despite its advantages, the Deep Web presents several cybersecurity challenges.
- Organizations use intranets for internal communication and documentation and for hosting internal online tools.
Understanding The Deep Web Vs Surface Web
Unlike the Dark Web, which requires a special web browser called Tor, you can use any browser to get to the Deep Web. While the deep web serves a largely communal and educational purpose, the dark web often invites danger, fraud, and crime. Each layer of the internet requires users to approach their activities with mindfulness, adopting necessary precautions to protect themselves against potential threats.
Unlike the dark web, which necessitates anonymizing browsers such as Tor, the deep web is accessible via standard web browsers. However, most deep web content is gated behind login credentials, subscription fees, or institutional access permissions. These safeguards prioritize the privacy and security of sensitive information, ensuring that only authorized users can interact with the data. The term “Deep Web” conjures images of encrypted chatrooms, digital espionage, black markets, and hidden societies. Pop culture and news stories have blurred its meaning with the “Dark Web,” a more secretive and often illicit subset. But in truth, the Deep Web is not inherently mysterious or malicious—it is simply the part of the internet that lies beyond the reach of traditional search engines.
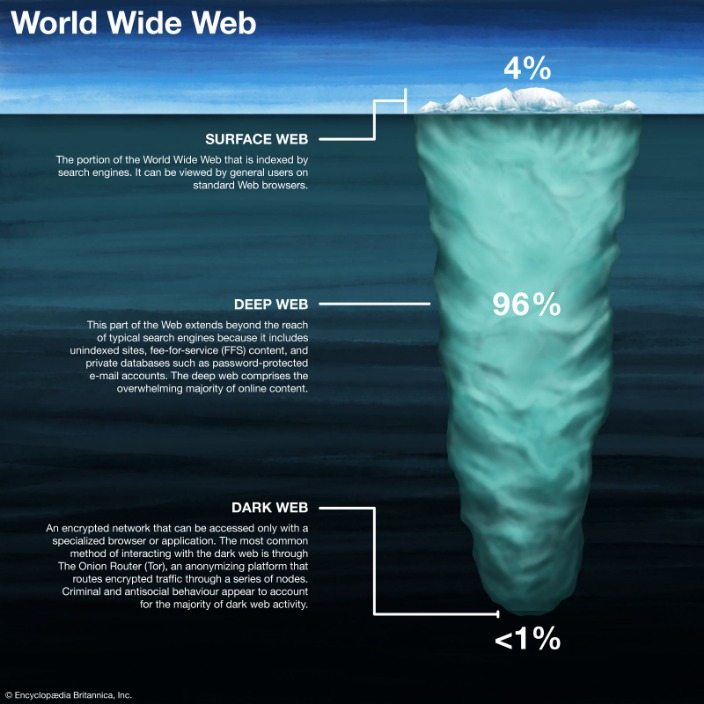
How Large Is The Deep Web?

The tools to carry out the cyberattack may have been bought off a dark web marketplace, but the attacker would propagate the attack using mediums available on the standard web (such as email or chat). Some experts peg the size of the dark web at approximately 5% of all the content on the internet. The architecture of the dark web features some key elements that make it an anonymous sanctuary for censured activities. NordVPN is a high-performing VPN we frequently recommend to our readers, and 1Password is a secure password manager we have reviewed in detail. Both of these are excellent utilities you can try without second thoughts. There are many, but my personal favorite is ProtonVPN (free version available).
Users leverage these platforms to organize protests, whistleblow, share survival guides, or share files P2P. Some markets even sell privacy tools, but you are more likely to run across counterfeit prescription pills and stolen identities. Keybase is a fantastic onion website that lets you cryptographically bring your different online identities together. Look no further if you want good music while navigating the dark web. Moreover, due to its popularity, many copycats of the Hidden Wiki exist.



