Among those was Kyle Fox, 26, of the United Kingdom, who was sentenced to 22 years for raping a 5-year-old boy and appearing on Welcome To Video sexually abusing a 3-year-old girl. The most likely places for such behavior to start include social media, messaging apps, and chat rooms – including on gaming devices. A youth may be encouraged to give personal details, to go off into a private chat, and also to use video chat. Although a relationship may be initiated in a chat room or social networking site, they can continue through text, email, or through the use of other apps.
Though his codefendants didn’t disclose prior instances of abuse, the attorney called it “wildly unlikely” that their involvement in the website was their “first rodeo.” The European Commission unveiled a new internal security strategy called ProtectEU to better detect cyber threats, fight serious and organised crimes, and share intelligence across the region. “While many people believe they can hide in these corners of the dark web, the online world is not anonymous,” Det. Erik Bjarnason of the Alberta Law Enforcement Response Team’s Internet Child Exploitation unit told Global News.
Child Sex Abuse Site Creator Jailed
The Internet Watch Foundation’s powerful new tool for small businesses and startups. Designed to detect and stop known illegal imagery using advanced hash-matching technology, Image Intercept helps eligible companies meet online safety obligations and keep users safe. In a review of 12,000 new AI-generated images posted to a dark web forum over a one month period, 90 percent were realistic enough to be assessed under existing laws for real CSAM, according to IWF analysts. She sentenced McIntosh to 55 years in prison — 15 years fewer than prosecutors recommended, and 30 more than his defense attorney did — and promised to recommend that he undergo psychosexual therapy in prison, “which he is in dire need of.”
FBI: Exploit That Revealed Tor-enabled Child Porn Users Wasn’t Malware
He has covered Washington for two decades, earning 20 Emmy and Edward R. Murrow awards. Rosenstein possessed such a large quantity of abusive images, he needed to store some on a server he used to run his business, according to the Justice Department. Their search warrant was so important to the bureau that it was approved by the FBI director himself. When the agents breached Spearman’s door with tactical explosives, Spearman fought back, tussling with the agents as three of his handguns remained barely out of reach. The FBI managed to handcuff and arrest Spearman, a high-value arrest, in what a top Justice Department official called “one of the most successful” prosecutions of its kind. As I’ve previously said, it’s a good idea to keep your interactions with the dark web to a minimum, unless you can absolutely trust the people you’re dealing with.
- Such behavior takes place virtually, without physical contact between the child and the person seeking to exploit them.
- While the material, commonly known as child pornography, predates the digital era, smartphone cameras, social media and cloud storage have allowed the images to multiply at an alarming rate.
- At the time, the department said it did not have enough funding to undertake the research and had no “time frame” for submitting a report.
- And in some cases cops defeated user attempts to hide their identities—such as a man who made payments using his mother’s name in Spain, a local news outlet, Todo Alicante, reported.
The Ticketmaster Data Breach May Be Just The Beginning
Delzotto told CBS News, “Few people would have envisioned how (child abuse materials) would permeate the internet, the way it has today.” The Operation Grayskull investigation launched in 2020, when law enforcement agents noticed a spike in traffic to a dark web site suspected of hosting child abuse material. The dark web child abuse sites eventually attracted more than 120,000 members, millions of files and at least 100,000 visits in a single day, according to an FBI official who spoke with CBS News. It’s a place where you’ll find data leaks and illegal trades, but also legitimate, legal online activities users want to carry out without attracting the attention of law enforcement agencies or governments. It’s a part of the internet that’s less regulated and more shadowy, for better and for worse.
ICE Used ‘stingray’ Cell Phone Snooping Tech Hundreds Of Times Since 2017
Tech companies are legally required to report images of child abuse only when they discover them; they are not required to look for them. In interviews, victims across the United States described in heart-wrenching detail how their lives had been upended by the abuse. Adults, now years removed from their abuse, still living in fear of being recognized from photos and videos on the internet. And parents of the abused, struggling to cope with the guilt of not having prevented it and their powerlessness over stopping its online spread. Children, some just 3 or 4 years old, being sexually abused and in some cases tortured. In order to make the AI images so realistic, the software is trained on existing sexual abuse images, according to the IWF.
October 2023 Report Summary
Some state lawmakers, judges and members of Congress have refused to discuss the problem in detail, or have avoided attending meetings and hearings when it was on the agenda, according to interviews with law enforcement officials and victims. The year was barely half over, and Chief Farnsworth’s team had already conducted about 150 such raids across Utah. The specially trained group, one of 61 nationwide, coordinates state and regional responses to internet crimes against children. Mr. Shehan, the vice president, said such disclosures might discourage tech companies from cooperating with the center. A Microsoft spokesman said that the company had only limited information about offenders using the search engine, and that it was cooperating as best as it could.
Just The News In Your Inbox
‘Protected by Mediocean’, a leading solution for holistic ad verification has joined the Internet Watch Foundation to strengthen safeguards in the digital media supply chain and help protect children online. McIntosh, shackled in orange prison garb, scanned the empty seats reserved for his family as deputies led him from the courtroom. His hearing came one day before the man who killed Abby and Libby was sentenced to prison, too. At its conclusion, Cannon called McIntosh’s propensity to abuse children the most severe she had ever seen.
Support Just The News
Bing was said to regularly submit reports that lacked essential information, making investigations difficult, if not impossible. Snapchat, a platform especially popular with young people, is engineered to delete most of its content within a short period of time. According to law enforcement, when requests are made to the company, Snap often replies that it has no additional information. One image showed him orally raping a 2-year-old; another depicted a man raping an infant’s anus.
- While any child at imminent risk remains a priority, the volume of work has also forced the task forces to make difficult choices.
- We encourage you to share our campaign using #ThinkBeforeYouShare and by following, liking and sharing the campaign on our social channels.
- If that view gains traction, Fourth Amendment challenges about searches and seizures by the government could change how the center operates and how tech companies find and remove illegal imagery on their platforms.
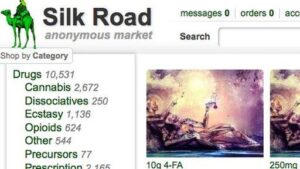
- The site was “one of the first to offer sickening videos for sale using the cryptocurrency bitcoin,” the UK’s National Crime Agency said.
German prosecutors announced Monday they have busted one of the world’s biggest international darknet platforms for child pornography, used by more than 400,000 registered members. Find out why we use the term ‘child sexual abuse’ instead of ‘child pornography’. Offenders were also documented sharing advice and even AI models fed by real images with each other. In one raid by German and Dutch authorities, nearly 72,000 videos of child sexual abuse were recovered. Additionally, there is also likely to be a traumatic impact on moderators and investigators having to view abuse images in the finest details to identify if they are “real” or “generated” images.
A nine-count indictment says 337 people in 24 U.S. states and 11 countries, including eight individuals in the Washington, D.C., area, were arrested and charged with operating or using the site. There can be a great deal of pressure for a young person to conform to social norms by engaging in sexting, and they may face coercion or manipulation if they go against the status quo. It is important that youth know that they have the ability to say NO to anything that makes them uncomfortable or is unsafe. They should also be informed about the risks of sexting so that they have the language to make safe decisions and navigate this in their own peer group. Anglia Ruskin University researchers say forum members are teaching themselves using non-AI images.
Congress has regularly allocated about half of the $60 million in yearly funding for state and local law enforcement efforts. Separately, the Department of Homeland Security this year diverted nearly $6 million from its cybercrimes units to immigration enforcement — depleting 40 percent of the units’ discretionary budget until the final month of the fiscal year. Many of the survivors and their families said their view of humanity had been inextricably changed by the crimes themselves and the online demand for images of them. The National Center for Missing and Exploited Children (NCMEC) analyzed the site’s content, including more than 250,000 unique videos, according to the Department of Justice. Adults may offer a young person affection and attention through their ‘friendship,’ but also buy them gifts both virtually and in real life.