There’s no need to worry about linking personal information or banking details to your order. Plus, cryptocurrency transactions are fast, reliable, and protected by blockchain technology for added security. We believe in doing it right the first time, so you never have to worry about second-rate products or wasted money. When you choose us, you’re choosing reliability, craftsmanship, and peace of mind. Because let’s face it, when it comes to fake IDs, cutting corners is not an option.
Royal Class Cards
One option is to not allow photo uploads of ID documentation when verifying customer identities. Instead, they should require new users to snap a photo of the document in real time. Since services like OnlyFake provide images of bogus documents, not physical copies, fraudsters would be unable to pass through ID verification with just an image. Certain businesses rely on identity verification systems to process the large volume of new account sign-ups they receive. They can also implement a number of checks and balances to combat fake IDs, even if they aren’t checking each one by hand.
BitLaundry: For All Your Bitcoin Washing Needs
While stronger document checks are important, many experts see the long-term solution as moving away from traditional identity documents altogether. Verifiable Credentials (VCs) and Decentralized Identity frameworks offer a more secure and privacy-focused alternative. One example is OnlyFake, an underground website known for offering realistic digital IDs in just a few clicks.
DeepHole – 10x Your BitCoin In 24 Hours

A default “expiry time” must be set, offers multiple time-frames to choose from, however, the minimum is 5 minutes the maximum being 1year. Another dark web apple store that is offering iPhones, Watch, Airpods, iPad and Macbook. They supports Escrow payments that’s make them trustable.
GCking Market: #1 Gift Card Shop

It’s been a constant back-and-forth between cybercriminals and law enforcement, with each new site trying to be smarter and more secure than the last. In 2019, there were approximately 8,400 active sites on the dark web, selling thousands of products and services daily. As of 2020, nearly 57% of the dark web was estimated to contain illegal content, including violence and extremist platforms. Don’t forget to include links to mirrors.txt of the service you want to list, so that I can verify them before listing. Fake IDs pose significant challenges in today’s society. Recognizing them is crucial for individuals in retail, bars, and anyone concerned about identity fraud.
When you connect to Tor, your internet activity is sent through the Tor network, anonymizing your Internet activity so it can’t be snooped on, and so that you can access websites that may be blocked in your country. Some states view black and white photos as more resistant to alterations or forgery than color photos, leading them to choose black and white images for increased ID security. Economic factors can influence the decision to opt for black and white photos. Producing these images can be more economical than printing color photos, prompting some states to prefer them as a cost-saving option.
These counterfeit documents include driver’s licenses, state identification cards, passports, social security cards, birth certificates, visas, and even professional certifications or diplomas. The dark web, a concealed portion of the internet accessible only through specialized software like Tor, provides an ideal platform for such illicit trade due to the enhanced anonymity it offers buyers and sellers. Even more alarming is the recent rise in synthetic identity fraud—a fast-growing form of financial crime where real and fabricated information are blended to create new, non-existent individuals. Fraudsters often use stolen Social Security Numbers (often belonging to children, the deceased, or those not actively monitored) combined with fake names and birthdates to build completely new credit profiles.
Identitycom
Banks and financial services providers use digital verification platforms equipped with facial recognition technology, biometric checks, and database verification. Any discrepancies trigger internal security protocols, flagging suspicious accounts for further scrutiny or reporting to authorities, potentially resulting in legal action against account holders. Purchasers ranged from underage individuals seeking entry to clubs and bars to criminals engaging in identity theft and money laundering schemes.
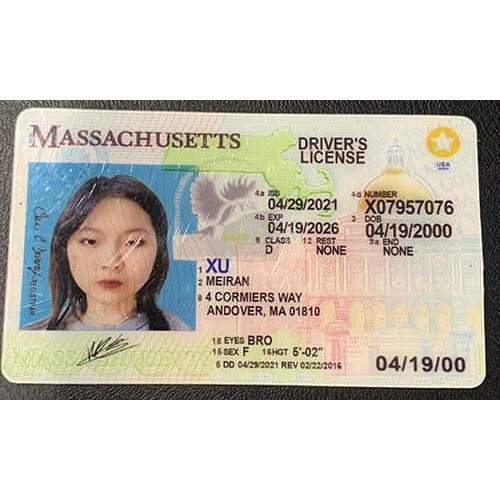
Common Types Of Fake IDs
Here is another financial marketplace operated by a group of highly skilled hackers (electronic and computer expert). In 2009, they launched website on darknet to sell credit cards, bank accounts, PayPal transfer, and western union. In fact, they claims that they sells only checked and valid accounts.
Often, the images used to print the background graphics are low resolution and blurry. In many cases, close scrutiny of the facial image of the card holder will show obvious seams where they were glued or photo-shopped on top of the background. Additionally, communities facing rampant document fraud often see declining public trust in institutions, businesses, and even interpersonal relationships. When citizens perceive that fraud is widespread or tolerated, social cohesion weakens, damaging overall community resilience and stability. Moreover, widespread usage of counterfeit documents can lead authorities to implement increasingly stringent security measures, which often inconvenience or infringe upon privacy rights of law-abiding citizens. Additionally, increased enforcement measures necessitate higher governmental expenditures funded through public resources, placing an economic burden on taxpayers.
- It’s a forum that teaches how to manufacture industrial-grade drugs.
- If you are looking for dark web sites which offer hacking services, below .onion sites are for you.
- Hidden Cards allows you to buy cards which have a minimum $3500 balance and costs $100.
- Topics cover everything from lab setup, production to encryption, marketing and legalities.
- PayPal accounts are listed with account balance, account price, your profit and account location.
- In the workforce, this risk extends to employment fraud.
Here, you’ll find links to various resources, including educational archives, private forums, anonymous services, and more. Beyond abstract ethical considerations, document fraud frequently results in direct harm to individuals. Identity theft victims, for instance, suffer severe personal, financial, and psychological damage, often spending years attempting to restore their credit histories, reputations, and emotional security.

Fake IDs and passports are predominantly sold through hidden online marketplaces accessible via the dark web. Launched in September 2022, Torzon Market operates on the Tor network and features over 11,600 illegal products, including drugs and hacking tools. It enhances buyer transparency by importing vendor feedback with PGP proof. Torzon offers a premium account option for additional benefits and is valued at approximately $15 million, accepting payments in Bitcoin (BTC) and Monero (XMR). Wolf Bank Hacker Group is operated by a group of hackers with over 25 years of experience.
Some airports have already moved away from manual ID inspections entirely, and financial institutions are increasingly turning to automated alternatives. In the workforce, this risk extends to employment fraud. In 2024, U.S. authorities indicted 14 North Korean IT workers who used stolen and fabricated identities to obtain remote jobs at American companies. While not all of the documents were created using AI, the case highlights how digital identity fraud can be used to access sensitive systems. Similar tactics may soon become accessible to less sophisticated actors as these tools spread more widely. Some bad actors go a step further by blending real and fake information to create synthetic identities.
AI-generated Fake Passports
Here you can get US dollars, Euros, and GB pounds in cheap price. Because there are no passwords, your username also acts as your password. To check your e-mail, you simply enter your username, e.g. , and you’re logged in.



