However, that’s just one of the main differences between the two — we’ll discuss more in this guide. We’ll dissect the dark web and the deep web to reveal how they work and their underlying technologies. We’ll also highlight the risks and show you how to access each section of the internet without jeopardizing your digital security or privacy. Simply accessing sites that are not indexed or otherwise publicly available is not illegal. It could, however, be illegal to misuse or steal information found on deep websites.
Best Dark Web Sites 2025 – Detailed List
The affiliates distribute the ransomware packages through the dark web. These attacks often include stealing victims’ data and threatening to release it on the dark web if the ransom isn’t paid. You could certainly go much deeper into the topic, but we hope the information provided here has given you a basic understanding of what the deep web/dark web are, how they function and why they exist. More importantly, you should now know how to access these hidden sectors of the internet at your leisure. We always recommend using a reliable VPN when accessing the deep web or dark web. That means that if your incoming traffic is routed through a node operated by cybercriminals, they can inject malware into the code of the response, without you ever knowing that it’s happened.
But before we get into that, it’s important to understand the differences between the surface web, deep web, and dark web. So, even though it does exist on the internet, Google doesn’t index any of these pages or content. You should stay away from everything labeled “porn”, “card skimming services”, “PayPal hacks”, “firearms”, “real fake IDs and passports”. Believe me – there are plenty to go around and each and every one of them are being kept under surveillance. Not to mention the fact that you’ll get exposed to some stuff that will definitely make you take several cold showers. Fortunately, in Hidden Wiki, every website is followed by a brief description so that the user knows what to expect.
- Threat actors also exploit vulnerabilities in your systems and software to gain access to them.
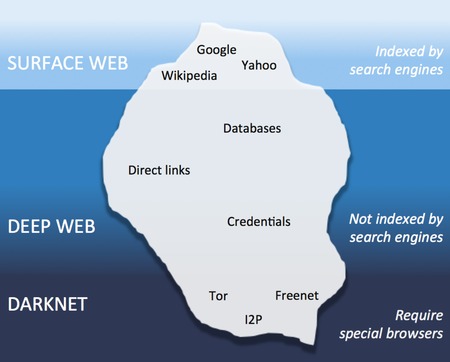
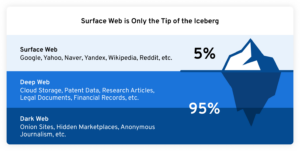
- The invisible web is made up of data and information that is not indexed and cannot be searched for by using traditional search engines.
- Cyber threat intelligence (CTI) helps organizations predict, understand, and defend against cyber threats, enabling proactive protection and reducing the impact of attacks.
- These are used to share and exchange information without public exposure.
Risks Of Accessing The Deep Web Vs The Dark Web
It’s somewhere Google and Bing don’t index, and you need special tools to get to it. Not all mass thefts of data facilitated by the dark web have been motivated by money. The publicizing of Snowden’s actions led to a global spike of interest in Tor and a resulting rapid expansion of the network’s user base.
What Kind Of Experience Do You Want To Share?
Opennet connections are easier to use, but darknet connections provide more security against attackers on the network. In opennet mode, the network will automatically assign you to other users on Freenet’s network. However, if you must buy items from the dark web, set up a secure, encrypted email with CounterMail or ProtonMail. For more information, read more about the most secure email service providers in my other post. Now that you’ve completed the download, it’s time to install the Tor browser on your device.
Method II – VPN Over Tor
Here are a few reasons why people rely on these varying parts of the web. Obscurity is cheap to implement, both financially and in administrative overhead. The unfortunate disadvantage is that the obscurity itself is illusory, and growing more so everyday, giving those who depend on it a false sense of security about their assets. Authentication is much better at preventing unauthorized access to resources.
It’s not easy to remove personal data from the Deep Web or Dark Web. Although most of this Deep Web can contain legitimate content that users can control with privacy settings and requests, much of the Dark Web contains data without the owners’ consent. People worrying about their data need to check their digital footprint periodically and seek services specifically offering data removal and monitoring services in order to minimize the potential risks. Browsing the Deep Web may be safe if users exercise precaution in accessing the web.
Commercial Services
One of Daniel’s impressive features was the built-in functionality that showed whether a particular dark website is online. After more than a year of no updates, the site admin shut it down, reasoning that he couldn’t keep the list of onion links up-to-date. If the VPN connection fails, the automatic kill switch will kick in, temporarily breaking your traffic. You should never use your personal information on the dark web anywhere else in your life.
- The Tor network was created to allow completely anonymous (with some additional precautions ) communication over the internet.
- This makes it even harder for third parties to see your email traffic.
- While some studies have claimed that illegal Bitcoin activity is as high as 44%.
- After more than a year of no updates, the site admin shut it down, reasoning that he couldn’t keep the list of onion links up-to-date.
- It comprises just a tiny fraction of the Deep Web, but its potential for misuse makes it a subject of significant concern for security teams and law enforcement.
Darknet Markets
TOR also lets users connect to websites in the surface and deep web anonymously, to prevent internet service providers from seeing what they are browsing. Hence, the deep web literally comprises all those parts of the internet that are not indexed by search engines. The kinds of content present in this region include private databases, medical records, academic journals, and other sensitive information that requires special permission to access. For example, every academic institution holds valuable resources within its online libraries that are important to its students and researchers who have legitimate access but not for public consumption. The deep web contains hidden content, such as private databases, government websites, and intranets. These parts of the internet require users to log in to access the data, and they consist of cloud servers that are protected with encryption and unlisted by search engines.

This allows people to access important information and services regardless of their location. Moreover, the deep web is not completely hidden and is a part of WWW (World Wide Web), whereas the dark web is completely hidden and cannot be accessed by any normal search engines. Have you ever wondered how come a result pops up on your screen when you type something on a search bar? Popularly known as the visible web or indexed web is a unit of the WWW (World Wide Web) that is open for general usage and can be accessible by anyone around the world.
If you have a legitimate or viable need to access the dark web, you’ll want to make sure you stay safe if you decide to use it. Some alleged services like the professional “hitmen” may just be scams designed to profit from willing customers. Reports have suggested the dark web offers many illegal services, from paid assassinations to trafficking for sex and weapons. However, you can still take illegal actions within Tor that could incriminate you regardless of the browser’s legality. You could easily use Tor in an attempt to pirate copyrighted content from the deep web, share illegal pornography, or engage in cyber terrorism.
Even free online services that are open to the public can be categorized as part of the deep web. For instance, banking websites require users to log in before viewing their account statements. Even email services such as Gmail are part of the deep web, as search engines cannot access the data on the platform. The deep web is the internet portion that cannot be indexed by web search engines, such as Google or Bing.
Check out these best onion sites to access the dark web securely and anonymously. The illicit activities of fraudsters are happening across the Gray, Deep, and Dark Web. But the real battle against fraudsters is on the Deep and Dark Web, where tracking their activity is much more difficult.