
Here are some things to keep in mind while browsing your favorite dark web websites. Apparently, Hack-Rent-A-Hacker’s most popular ‘service’ is Facebook account hacking – figures! Anyway, if you’re in this sort of thing, someone can help you get inside a Facebook account for 250 euros. It goes without saying that I do not advise you to seek this sort of service. No info is available on the explored institutions or how these sections can be accessed.
With each random server, your traffic bounces off, and a layer of encryption gets added. These layers upon layers give this network its iconic “onion” name—as the onion itself has layers upon layers. This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacyRadar.com page. However, it has a sneak peek, easy guide steps, and/or a quick list providing quick in-page navigations and easily-found answers if desired.

Wer Ist Der Eigentümer Von Tor?
This means you will get a VPN’s security and enjoy the anonymity of the Tor network simultaneously. Immediately close your entire Tor Browser window (not just that active tab). Note that engaging with the content in any way is not only distressing but could also put you at legal risk. This is because law enforcement often actively monitors these sites.

The site has a simple interface and offers filters to find books. However, not all books on this site are legally available, so they don’t have copyrights. That means you may violate copyright laws while downloading books, so use a VPN to protect yourself from any legal repercussions if you have a dire need to use it. Sci-hub is a helpful dark web platform for those looking to access important research blocked by a paywall. You can access almost any published paper that would have otherwise been hidden behind a paywall.
For several years, Yahoo was at the apex as the internet’s best web service provider, offering… The US government created the dark web to help its spies communicate and exchange information securely. The Onion Router (Tor) also made the technology available in 2002. It is a relatively new provider but offers better features than most established VPNs. NordVPN is one of the best VPNs to combine with the Tor browser whenever you want to surf dark sites. It offers top-of-the-line security and fast speeds for a smooth browsing experience on the dark web.
🛡️ Warum Sie Ein VPN Brauchen, Um Das Darknet Zu Erkunden
They know how to process the information and get it to the correct law enforcement agencies internationally. You risk being targeted for attacks if you explore the dark web without protection. The threat can extend to your entire network of devices connected to the internet.
Does Tor Hide Your IP Address?
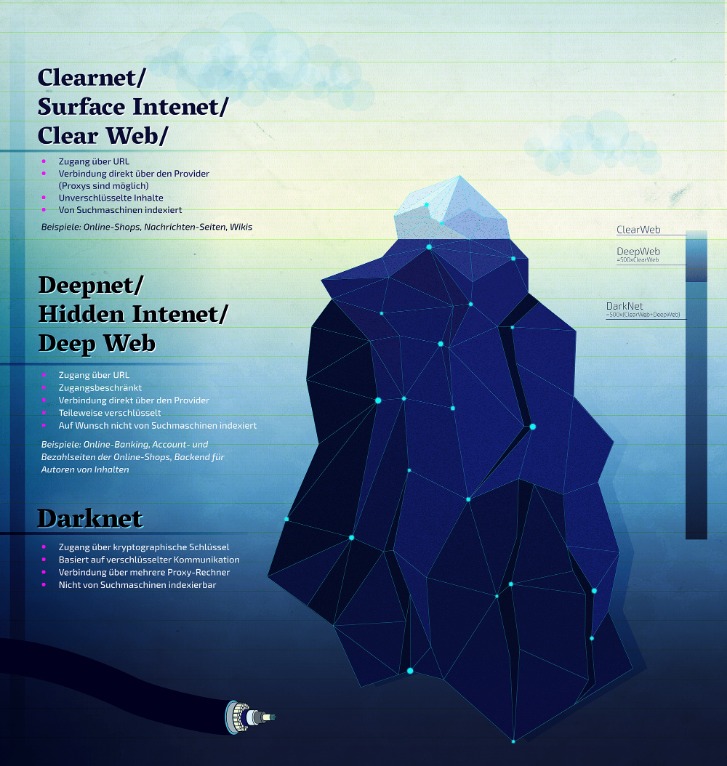
It is easily accessible by the general public and requires no special configuration. You can access it with regular web browsers and search engines. You can find sites like Facebook, Wikipedia, e-commerce sites, YouTube, and more here.
- SecureDrop is a secure hub for journalists and whistleblowers to interact and trade vital information.
- Unlike other search engines, it does not collect or share web activities and personal data of users.
- It will make your VPN activities seem like normal traffic, so you can use an uncensored internet.
- Thankfully, you don’t need to use your official name or email; just use a fake username (we tested it successfully).
In many places, including the U.S., the UK, and the EU, accessing the dark web is legal for legitimate purposes. However, many sites on the dark web host illegal content or activities, and engaging with those can lead to serious legal consequences. In some countries, like Russia or China, dark web access itself may be blocked or penalized. Norton VPN fortifies your internet connection with ultra-secure AES-256 encryption, masks your IP, and never logs your activity. Proton Mail is an anonymous email service that operates an onion site.
Social Networks

The provider also offers a dedicated CyberSec suite that prevents annoying ads and blocks malware and trackers. Law enforcers can use custom software to infiltrate the dark web and analyze activities. You could be monitored closely even if you are not doing anything illegal.
Sicherheit Im Internet
When you try to connect to a .onion website, Tor will route your traffic through three or more randomly chosen nodes before it reaches your destination website. Each server adds a layer of encryption, and this layered system is what lends The Onion Router its name. This is also why the sites on the dark web are called Tor links.
RiseUp is a top dark web website that offers secure email services and a chat option. It was created in 1999 as a secure communication platform for people and groups working on liberatory social change. The platform is protected from government interference and malicious attacks to protect the user.
- In most cases, whistleblowers have sensitive information about the government or a company.
- However, this feature is only available on iOS, Android, and Windows.
- On the dark web, traffic is routed through multiple server nodes that don’t log activity, obscuring the user’s origin and enabling anonymous communication.
- Many reputable websites and news outlets like ProPublica and SecureDrop often share official domain addresses of onion sites on their pages.
- These layers upon layers give this network its iconic “onion” name—as the onion itself has layers upon layers.
Mit Dem Tor Browser Surfen: Die Beliebtesten Seiten Im Darknet
However, you should not see it as an opportunity to engage in illegal activities to avoid trouble with authorities. The Camouflage Mode is intended for people living in countries with heavy internet censorship, like China. It will make your VPN activities seem like normal traffic, so you can use an uncensored internet.
Simply put, accessing and browsing the dark web is perfectly legal. For example, it maintains your privacy and enables you to access untraceable content and services. Another essential security feature is that all incoming and outgoing data from the app is encrypted, including any private and public keys involved. The US Naval Research Laboratory developed The Onion Routing (Tor) project in the late 90s.
CORE PROTECTION

It also offers works of art, course material, and audiobooks for download. Keybase also offers extremely user-friendly secure chat and file-sharing services through its app. Based in Switzerland, ProtonMail is an encrypted email service that is very popular with cryptocurrency enthusiasts. The process costs a fee, but unlike other “tumbler” or “mixing” services, there is no risk that Wasabi or any of its users could scam you out of your coins. I have to admit to having a soft spot for Tunnels, an onion website about underground “urban” exploration. Apart from having that “As above, so below” vibe, Tunnels is a great source of info for users who are into dark urban history.
Dark Web Websites: 10 Onion Sites To Explore
Careful though, because many ‘users’ reported malicious links and redirects while perusing Sci-Hub. It is important to note that the people or journalists who use ProPublica to spread their truth recognize the risk of doing so. As a result, we want you to stay safe and anonymous by using a paid VPN service whenever you surf this dark web platform. DuckDuckGo is a helpful search engine available on the Tor that allows you to browse the dark and regular web anonymously. Unlike regular search engines such as Google, Yahoo, Bing, DuckDuckGo does not store your data, ensuring complete anonymity. OnionLinks is a library of dark web links, most importantly, active links.



