Selecting the right browser for accessing the dark web is crucial, as it significantly impacts anonymity, security, and overall usability. Here’s a detailed analysis of the top browsers available in 2025, each uniquely suited to different types of users and requirements. Staying safe on the unregulated dark web requires vigilance, and its seedy reputation, fostered by controversy like that surrounding Silk Road, is well-earned. If you want to learn all about privacy protection or cryptocurrency, the dark web has plenty to offer. There are a variety of private and encrypted email services, instructions for installing an anonymous operating system and advanced tips for the privacy-conscious. We don’t want to leave you with the impression that everything on the dark web is nefarious or illegal.
FBI’s Internet Crime Complaint Center Reports $16 Billion In Losses For Americans Due To Scams And Fraud
To improve your local-language experience, sometimes we employ an auto-translation plugin. Please note auto-translation may not be accurate, so read original article for precise information. We’re a nonprofit organization and rely on supporters like you to help us keep Tor robust and secure for millions of people worldwide.
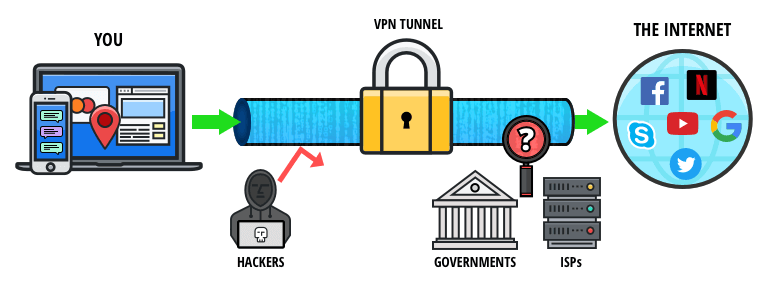
Advantages Of VPN Over Tor
There are other ways for spies, hackers or other adversaries to target Tor. Lewis points to the “first contact problem”, when an attacker spots when someone moves from non-private tools to private ones, noting it’s been used to identify whistleblowers. On the surface web, you can contact your credit card company or law enforcement for help. But the dark web operates like the Wild West—no rules, no protection. Threat actors also exploit vulnerabilities in your systems and software to gain access to them. So, you should also make sure that your system’s operating system and other installed software are patched with the latest updates.
The VPN provides data encryption and routes your data through remote servers to help mask your IP address and location. Thus, it successfully prevents anyone from snooping during your activity. The VPN has a vast and well-established network, with 6,000+ servers spread across 111+ countries. When exploring the deep web, this VPN will offer fast and stable connection speeds on most servers.
- Install Tor Browser from the official website, adjust security settings to “Safer” or “Safest,” and only use trusted onion links from verified directories.
- Check around with other users and ask if they know anything about the new marketplace.
- When you’re done surfing or shopping on the dark web, don’t forget to shut down Tails.
- This can lead to incrimination for other activities later in life.
- Since .onion URLs can be complex and random, consider bookmarking reliable sites in Tor for easier access.
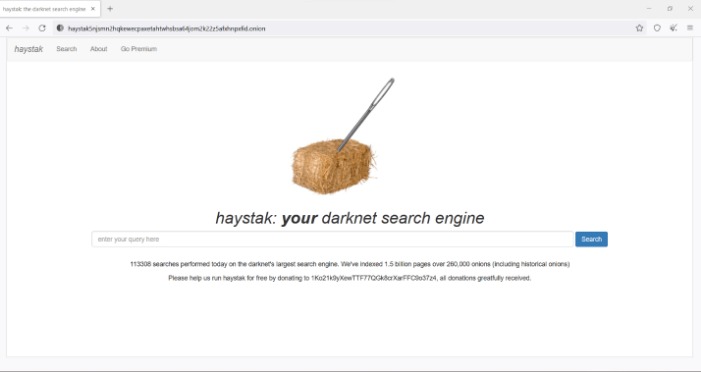
Is There A Search Engine For Onion Sites?
Due to compatibility issues and technical restrictions imposed by Apple, Tor browser isn’t available on iPhones that haven’t been jailbroken. Onion Browser is typically the go-to alternative for iOS devices and is powered by Tor. Prior to Keeper, Darren served as an advisor to JiWire, now called NinthDecimal.
Use A VPN To Stay Safer On The Dark Web
While the Dark Web might be home to a wealth of valuable information and services, it’s also notorious for being incredibly dangerous. Many websites that operate within the Dark Web are home illegal drug trafficking, human trafficking, child pornography, theft, gore and much more. The Hidden Wiki is a huge directory that provides links to Onion websites with various services, secure email, secure social networks and more. Tor’s browser connects to what’s called the Tor network, which establishes an anonymous connection that protects against network surveillance and tracking. In addition to being able to access any website you can in a standard browser, you can also access Dark Web URLs that end in .onion.
You’ll notice that some websites’ loading times are longer when using Tor. We can say the same about private networks belonging to companies and other entities. Some hospitals even have classified medical records you can’t access just like that. Ensure that you’re aware of what is permissible in your jurisdiction. Do not use any personally identifiable information on the dark web. Use aliases and avoid any activity that might reveal your identity.
What Is The Dark Web Search Engine?
Without a VPN, you could be putting yourself at risk of being hacked or scammed. A VPN allows a user to encrypt all internet traffic traveling to and from his or her device and route it through a server in a location of that user’s choosing. A VPN, in combination with Tor, further enhances the user’s security and anonymity. Again, we can’t emphasize enough that security and anonymity are paramount to those on dark websites.
Ensuring Security And Anonymity
That said, it can be difficult for users to find the material they are looking for on the dark web. Addresses tend to be a mix of random numbers and letters, making them challenging to remember or access manually. Addresses also change frequently due to the transient nature of many dark web actors. Finally, because the dark web routes all traffic through a series of proxy servers, which are operated by thousands of volunteers around the world, the search process is typically very slow.
(Optional) Change The Tor Exit Server
DuckDuckGo is the best dark web search engine, as it offers an excellent user experience akin to surface web search engines. Its effectiveness in scouring the shadowy depths of the dark web can be likened to what Google does on the surface web. The Tor network’s principal benefit is that it routes your traffic through numerous servers, wrapping it in several layers of encryption. This makes it difficult for interlopers to monitor the traffic or trace any legal or criminal activity back to you. One study found that only 6.7% of Tor anonymity network daily users — a cohort that comprises mostly dark web users — connect to onion sites used for illicit activity. This essentially means that over 93% of Tor daily users use the dark web for legitimate reasons.
This malware can be concealed within seemingly harmless files, and even simply visiting a compromised website might lead to an unintentional download and installation of malicious software. The risk of infection is considerably higher compared to the surface web due to the lack of regulation and security oversight. Despite these methods, finding reliable and safe onion links remains a significant challenge. The decentralized and often unregulated nature of the dark web means that there is no central authority vetting websites or ensuring their legitimacy.
However, it also supports legitimate uses like protecting free speech and accessing information in censored regions. Exploring the dark web can be a fascinating journey, but it requires the right tools and safety precautions. From popular options like Tor to specialized environments like Whonix and Tails, each dark web browser offers unique features to enhance your privacy and security. Navigating the dark web responsibly and cautiously will help ensure your experience remains secure.
However, VPN over Tor connections provide poor privacy, as Tor servers can collect your real IP address. Plus, very few VPNs support VPN over Tor connections — and the ones that do require you to perform an inconvenient manual setup. For the utmost privacy and security, combine Tor with a VPN connection. This encrypts your online traffic before entering the Tor network and shields your actual IP address.

Another is the Invisible Internet Project (I2P), which specializes in the anonymous hosting of websites on the dark web. Similar to using a standard web browser to access the open web, the act of using Tor or a dark web browser to access the dark web is not illegal in and of itself. It is illegal to perform illegal acts on the dark web, regardless of the level of anonymity provided by the platform. The safer option of the security settings only disables the JavaScript on websites that aren’t “https” protected, while the safest option disables JavaScript on all websites.



