That information is hidden simply because most users won’t find it relevant. Much of it is tucked away in databases that Google is either uninterested in or barred from crawling. Again, we can’t emphasize enough that security and anonymity are paramount to those on dark websites.
How To Access The Dark Web
I2P must be downloaded and installed, after which configuration is done through the router console. Then individual applications must each be separately configured to work with I2P. You’ll need to configure your browser’s proxy settings to use the correct port on a web browser.
The Ultimate 2025 Guide To The Tor Browser
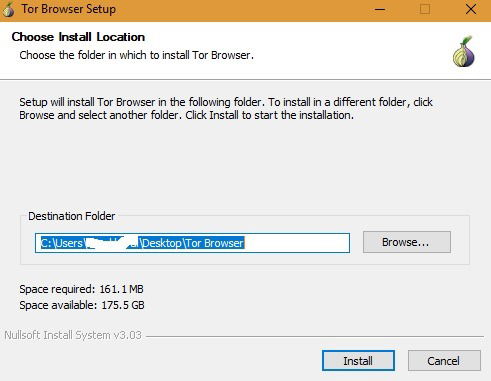
It might be because of the poorly maintained site or Tor’s slow speed because of the way it works. Either way, some sites take up to a minute or more to load, so don’t fret. If you’re prompted to connect, click the purple “Connect” button and wait for a few seconds. GNU IceCat stands as a modified Firefox browser dedicated to privacy and freedom, birthed from the GNU open-source project. Since their deadline wasn’t met for the closer of the sites a month later, the Impact team ascended to the dark web, where they started to publish the data. The child pornography site Playpen is one of the famous scenarios that resulted from the dark web.
Take Extra Security Precautions
It is a complete operating system dedicated to advanced security and anonymity. Whonix combines the Tor network, a Kicksecure Hardened core, and the security by isolation principle for a comprehensive privacy solution. Although the dark web is rumored to be hard to access, the Tor Browser is just a quick install away. With Tor installed on your PC or mobile phone, you’ll be able to browse active onion websites and protect your online privacy and anonymity. The Tor browser is designed to provide improved online anonymity and security.
Just for laughs and giggles, we visited this random pug’s ultimate guide to the dark web. You’ll notice that some websites’ loading times are longer when using Tor. From here, you can visit any Onion website and enjoy the dark web safely and without worries of ISP tracking and surveillance.
Can My ISP See That I Am Accessing The Dark Web?
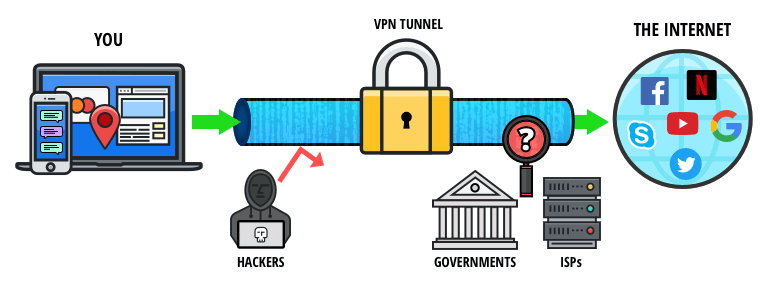
The middle node neither knows who you are nor where you’re going. You can use Tor without the browser, but the Tor Browser is the most popular and user-friendly way people interact with the protocol. Identifying specific individuals who use the dark web can be quite tricky. However, we advise connecting to one of our recommended VPN services to stay anonymous. For a number of technical reasons, it’s much faster and more reliable than Tor. The peer-to-peer routing structure is more advanced, and it does not rely on a trusted directory to get route information.
The Legal Aspects Of Dark Web Browsing
Tor Browser is the most popular option for accessing the dark web, known for its strong privacy and anonymity features. It’s designed to keep users’ identities hidden and to protect data from surveillance, making it an essential tool for dark web exploration. The above mechanism conceals your location and browsing activities from third parties like internet service providers (ISPs), advertisers, and web monitoring apps.
Download And Install Tor
We’ll go into great detail about the benefits and drawbacks of each browser, supported by a useful comparison table. Many countries, such as Qatar, China, Cuba, Russia, and Turkey, censor internet content promoting political dissent. The Darknet offers a place of free expression where not even a chunk of these limitations exists. They exchange sensitive information and data and, at times, have to risk their lives or that of their informant if they don’t share data under the safety of the deep web. Information on the dark web is not meant for public consumption, and the dark web protects personal data intended to be private.
The dark web also helps individuals communicate about or sell illegal items such as weapons, drugs, malware, etc. Many people see hacked information and stolen card data being sold on the dark web. However, you can find legitimate content and activities here, too.
Choose A Dark Web Search Engine

While this is good advice for any type of web browsing, be particularly careful not to offer up any personal details, such as your credit card info or email address. Use cryptocurrency to buy anything, and use a disposable email address for any type of communication on the dark web. Opennet connections are easier to use, but darknet connections provide more security against attackers on the network. But remember, it’s essential to take all the necessary and important security steps before entering such sites on the dark web. As mentioned before, your ISP and government institutions are not able to see what sites you visit on the Tor network, but they can probably see that you use Tor.
Change your passwords and watch out for suspicious activity on your credit reports. Your information might be on the dark web if it was exposed in a data breach, sold, or stolen by hackers. To check, you can use dark web scanning or breach detection tools like Avast Hack Check or LifeLock Breach Detection to search for compromised data. If found, take immediate steps to secure your accounts and personal information.
- We pay our bills online, check our bank statements, communicate via email, find information, and maintain a presence on social media.
- In this tutorial, we’ll explain how to access the dark web in complete privacy and cover a few more important factors to consider before starting.
- GetTor is a service that automatically responds to messages with links to the latest version of Tor Browser, hosted at a variety of locations, such as Dropbox, Google Drive and GitHub.
- By choosing the right browser and following best practices, you can safely navigate the hidden layers of the internet with confidence.

That said, the Tor Browser and a VPN make an excellent team for protecting your online activities from prying eyes, and provide optimal online privacy protection. While the Tor Browser hides your online browsing, it only hides your online activity through the Tor Browser. If you need to protect or enhance your streaming, gaming, or torrenting activities, a Virtual Private Network (VPN) is a much better option as a secure connection to the net. As I mentioned previously, using the Tor Browser will slow down your browsing. Since your traffic goes through a series of relays, getting encrypted or decrypted along the way, things slow way down. This means Tor is a lousy option for streaming video, online gaming, or downloading files (torrenting).
- Data privacy is one of the major civil rights issues of the 21st century, and it’s just smart to keep a lock on how much people and corporations know about you.
- Other dark web search engines include Not Evil, Torch, Haystack, and Ahmia.
- However, with the adoption of strict safety measures, practical anonymity can be attained.
- You can go on the dark web safely, use legal sites, and enjoy the experience without worries.
- It protects your real IP address even if Tor leaks, is easier to set up, and works with most major VPN services.
Plus, in some regions, accessing the dark web alone may raise suspicion or get you flagged for extra monitoring. The Tor Browser is the safest and most trusted way to access the dark web. That said, there are still some ways to protect yourself when using the Tor Browser.
While visiting any of the sites you find on those Wiki sites, do not maximize your browser, as it can help identify you by your monitor resolution. Tor Browser is available in multiple languages in a single multi-locale download, which can be changed using the menu in General settings. Get Avast BreachGuard for Mac to protect your privacy and keep your personal data from falling into the wrong hands. Get Avast BreachGuard for PC to protect your privacy and keep your personal data from falling into the wrong hands.



