
Mega Darknet Market is the dominant drug supply source for drug vendors on other darknet sites, holding a 63.4% share of that market. When looking at darknet drug markets serving Russia-based customers, Kraken Market captured 30.9% of market share, with Blacksprut and Mega Darknet markets closely following. As for drug markets serving Western customers, ASAP Market held a 25.0% share, followed by Mega and Incognito. The website allows visitors to view all the goods and services on display before they buy something. The quantity, price, and characteristics of the product are all provided. However, the platform lacks an advanced search option and a wallet-free payment option.
Threats To Personal Data
Whether it’s a torzon mirror masterpiece or a work in progress, our platform is the perfect place to share your torzon market creations with the world. Torzon mirror regularly hosts events, workshops, and meetups for torzon mirror enthusiasts of all levels. Check out our events calendar for upcoming gatherings in your area and join us for a day of torzon market fun and learning. Limited descriptions of products are given on the site and users are often re-directed to a specific Telegram channel of that vendor. The Telegram channels are either a channel for direct messages to the seller or are the seller’s support Telegram channel.
Darknet Marketplace Snapshot Series: Ares Market
The tools and techniques used to keep these platforms running reveal vulnerabilities that businesses must guard against. Companies today face constant threats of data theft, intellectual property leaks, and other dangers that originate from the dark web. Launched in 2020, Cypher Marketplace sells fraudulent documents, stolen credit cards, fake IDs, and malware. Its emphasis on user anonymity and document forgery makes it a core tool for identity fraud. Additionally, users face the constant threat of phishing attacks, malware, and other cybersecurity risks.
Search And Discussion
Ulbricht faced several serious charges, including distributing illegal drugs, running a criminal enterprise, hacking, trafficking fake IDs, and money laundering. In the end, he was sentenced to life in prison for running one of the largest and most scandalous dark web cases in history. If you take a quick look through darknet marketplaces, you’ll instantly notice an overwhelming supply of pirated content. We’re talking about even early access to unreleased music, leaked TV episodes, concert footage, and even popular video games before they officially drop.
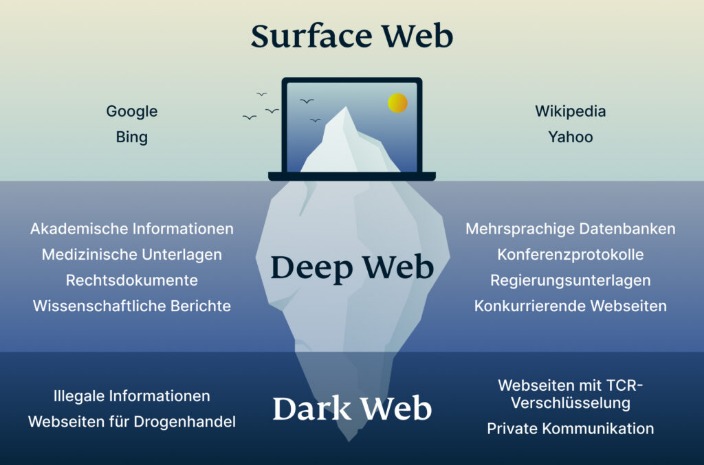
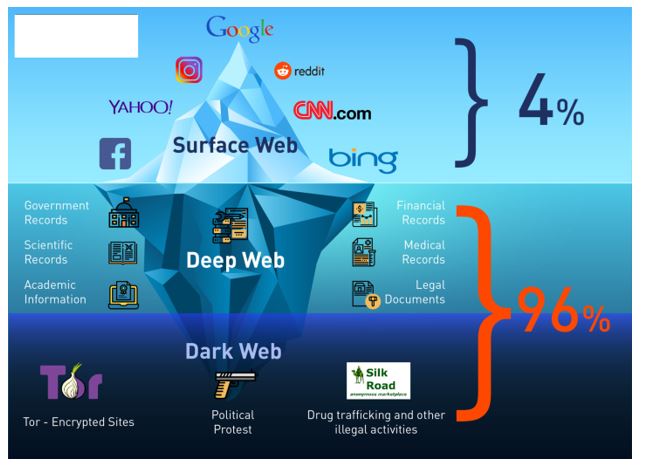
However, they aren’t visible on the open internet and require specialized browsers like Tor to access. This added layer of encryption masks users’ locations, making it nearly impossible to trace activity back to individuals. “Over the years some markets … developed a robust catalog of illicit services like money laundering, fiat offramping, and products that enable cyber-criminal activities like ransomware and malware attacks. One such sophisticated darknet market, Hydra, offered all that and more,” Chainalysis explained. TRM provides blockchain intelligence to help financial institutions, cryptocurrency businesses, and public agencies detect, investigate, and manage crypto-related fraud and financial crime.
How Do Dark Web Marketplaces Operate?
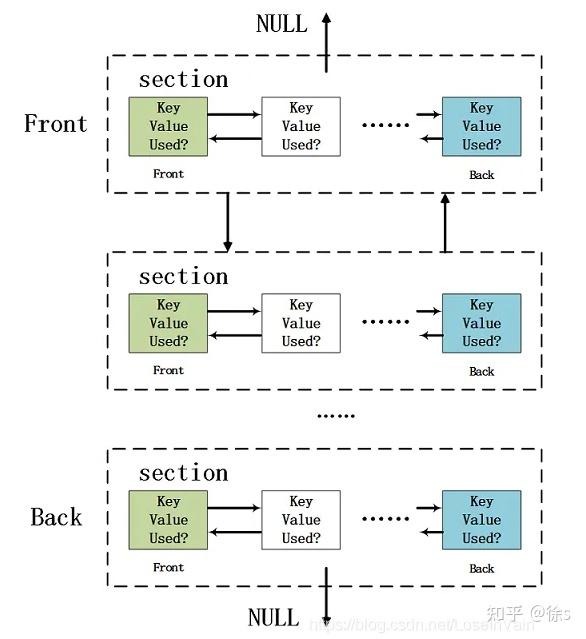
You can even use a secure email provider or a burner email address whenever you visit the dark web. The website has a sleek design and interactive user interface, making it the most preferred choice in terms of user experience. You can pay through Monera and Bitcoin using the escrow system or the traditional market account after making a purchase on this shop. It doesn’t use JavaScript, meaning the website won’t track your activities or exploit vulnerabilities. The website allows a personalized searching experience, where you can search according to your geographical location, country-specific, and keyword or price-specific search results. Since the dark web can be accessed through the Tor browser, use a VPN with the Tor browser to ensure increased protection.
This isn’t just a quick list; it’s the full scoop on what they offer, how they keep things tight, and why they’re worth your time—or not. Whether you’re new to the dark web or a vet who’s seen it all, you’ll find something here to chew on. Below, I’m breaking down each market with everything I’ve picked up—listings, quirks, the works. Others are looking for stolen data, hacking services, or even banned books and political content.
Emerging Fraud Schemes And Threats
Its commitment to privacy and reliability makes it a trusted choice in the darknet ecosystem. Nexus is a darknet marketplace designed to be the central point where trust, technology, and trade intersect. Known for its minimalist design and emphasis on security, Nexus provides a clean, distraction-free environment for users seeking stability and anonymity. With verified vendors, built-in escrow, and lightning-fast performance, Nexus remains a go-to platform for serious darknet users. Despite most darknet markets banning the sale of fentanyl in their terms of service, nearly all mainstream Western-facing markets have vendors that sell fentanyl-laced products. While it received a relatively small share of large retail purchases as shown in the previous chart, Abacus Market is one such example.
- Anyone considering engaging with these platforms must carefully evaluate potential consequences, exercise stringent security practices, and remain vigilant to minimize exposure to these significant hazards.
- From illegal goods and services to the consequences faced by both buyers and sellers, we’ll uncover the dangers lurking in these virtual underworlds.
- From items like drugs, fake ID cards, and hacked bank accounts to more complex offerings like human trafficking, these sites carry all the illegal activities you can think of.
- A crucial aspect of this work is blockchain analysis, where investigators track the movement of Bitcoin, Monero, and other cryptocurrencies through public and private ledgers.
- Nexus is a darknet marketplace designed to be the central point where trust, technology, and trade intersect.
These platforms offer end-to-end encryption, making it virtually impossible for third parties to intercept your messages or track your activities. Brace yourself, because we’re about to take you on a journey through the perilous world of darknet markets. An intuitive, user-friendly interface is crucial, especially given the complex nature of dark-web interactions. Users favor marketplaces with straightforward navigation, efficient search functions, and clear product categorizations. The ability to seamlessly communicate with vendors via secure messaging systems also greatly improves overall user experience. Experienced users typically prefer marketplaces with robust vendor rating systems, detailed feedback options, and transparent dispute resolution processes.
Inspector General Sites
University diplomas, Russian passports, residence permits, driver’s licenses, letters from the internal Ministry of Affairs, etc., are available on the market. There does not appear to be products such as weapons or listings that are human-related. The “rules” portion of the market explains that shops including human trafficking or “renting” shops are not allowed on the site. Staying ahead of cybercriminals requires more than reactive measures; it demands a proactive, systematic approach built on continuous improvement, risk awareness and adherence to proven security protocols. By integrating top-grade security into their operations, organizations can not only reduce their exposure to cyber threats but also reinforce trust in an increasingly data-driven world. Meanwhile, cybersecurity experts monitor the dark web, scanning for stolen data and emerging threats.
Founded in early 2023, shortly after major law enforcement operations shut down several competing platforms, Abacus quickly filled the void by prioritizing reliability, advanced security, and user anonymity. Marketplaces that maintain strict moderation policies—banning excessively harmful or exploitative products—also gain popularity among more ethically minded users. Ideal marketplaces support anonymous browsing through networks like Tor and I2P, utilize privacy-focused cryptocurrencies such as Monero, and implement measures to prevent tracking and transaction tracing. Platforms that provide clear guidelines for maintaining operational security (OpSec) and offer built-in tools for data obfuscation are especially favored. After that, many other marketplaces kept trying to take its place and become the top dark web market.
- So far, five million people have used the tool, and over 13,000 victims have been notified that their computer was infected, and received instructions to help them make their device safe again.
- When you are confident, absolutely positive that the vendor will still ship the product.
- The kinds of data for sale are typically PII (personal identifiable information) and credentials – information that can be used for fraud and scams.
- For a local machine configuration, he recommends a computer purchased for cash running Linux, using a local Tor transparent proxy.
In the first arc of the anime series Lupin the 3rd Part V, Lupin III steals digital currency from the “Marco Polo” darknet market. The months and years after Silk Road’s closure were marked by a greatly increased number of shorter-lived markets as well as semi-regular law enforcement takedowns, hacks, scams and voluntary closures. BidenCash and other exit-scam markets such as Torzon and Kingdom Market collapsed between 2022 and 2024. They used “free data dumps” and emotional marketing to build trust before vanishing—an enduring lesson in the risks of social engineering. BriansClub remains a long-standing credit card data shop since at least 2014.
Law enforcement agencies monitor many dangerous markets, and even anonymous browsing isn’t foolproof. Just visiting these sites can attract attention from law enforcement, especially if you interact with known vendors or download suspicious content. Even if you’ve never visited these markets, your personal and financial data might already be there, having been leaked through a data breach.



