It’s all about pills, weed, and the like—no heavy stuff like fentanyl, which keeps it chill. The site’s dead simple to use, and vendors leave feedback that’s actually helpful. I’ve noticed they’re big on local vibes—vendors tweak their stock for where you’re at. With 2FA and escrow, it feels safe enough, and it rarely goes offline.
The Decentralized Shift
For 2025, they’re teasing AI-powered search—could make digging through listings a breeze, which I’m hyped for since their catalog’s already hefty. The site’s unique—loads fast, looks sharp, and vendors get treated right, keeping turnover low. I’ve used it; shipping’s discreet—plain packages or DeadDrops—and uptime’s been flawless, rivaling Abacus.
Fraudulent Markets

The world of crypto now contains many coins and tokens that we feel unable to verify. In those situations, our Dexscan product lists them automatically by taking on-chain data for newly created smart contracts. We do not cover every chain, but at the time of writing we track the top 70 crypto chains, which means that we list more than 97% of all tokens. The total crypto market volume over the last 24 hours is $194.75B, which makes a 11.18% increase. The total volume in DeFi is currently $42.98B, 22.07% of the total crypto market 24-hour volume. The volume of all stable coins is now $185.99B, which is 95.50% of the total crypto market 24-hour volume.
Silk Road And Early Markets
TRM provides blockchain intelligence to help financial institutions, cryptocurrency businesses, and public agencies detect, investigate, and manage crypto-related fraud and financial crime. TRM’s risk management platform includes solutions for transaction monitoring and wallet screening, entity risk scoring – including VASP due diligence – and source and destination of funds tracing. These tools enable a rapidly growing cohort of organizations around the world to safely embrace cryptocurrency-related transactions, products, and partnerships. Individuals began using the darknet to pseudonymously sell illegal content without face-to-face interaction. Over time, ambitious individuals created infrastructure for these transactions, where for a fee, sellers have access to a digital ‘storefront’ to sell their products in a centralized marketplace.
How Do I Verify Onion Routing Links?
Moreover, the layers of encryption and the bounce of your data from node to node effectively mask your IP address, enabling online anonymity. It allows access to the .onion sites on the dark web that you won’t find using a regular browser. In addition to its emphasis on stolen credentials, 2easy Market offers a variety of cybercrime tools, such as hacking services, exploit kits, and other resources for conducting cyberattacks. The market frequently makes headlines for releasing massive troves of stolen data, often as a way to advertise its services.

The platform supports Monero (XMR), Bitcoin (BTC), and several others to hide identities. The most important thing is to ensure that you never click on links that you’re not sure of their source. Also, it should be common knowledge not to share personal information online. Perhaps, hiring a hacker can feel impossible, but it’s a genuine threat that you need to be aware of. In fact, several businesses can use that service to get rid of competitors, or individuals can use it to gain access to personal information about someone. In the first arc of the anime series Lupin the 3rd Part V, Lupin III steals digital currency from the “Marco Polo” darknet market.
What Is The Cost Of Stolen Data On The Darknet Market?
Major active platforms include Abacus, Russian Market, BriansClub, and Exodus. Law enforcement takedowns, such as Archetyp, demonstrate both impact and adversary adaptation. For cybersecurity professionals, focusing on payment methods, vendor migration, and marketplace specialisation offers the most effective path to actionable intelligence. Governments must adapt rapidly, crafting agile legal frameworks that balance innovation with accountability. Private cybersecurity firms must strengthen partnerships with regulators to track illegal transactions and monitor emerging threats.
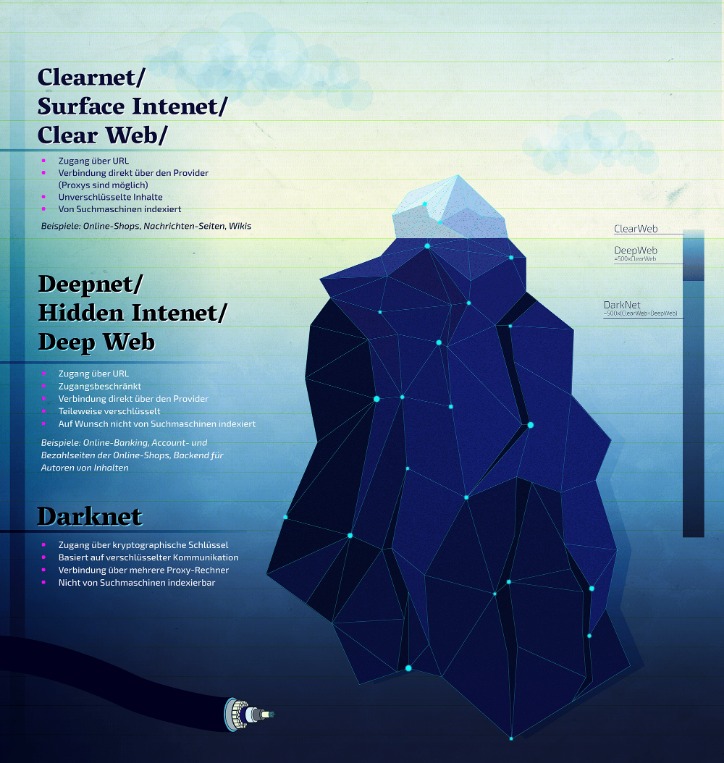
KEY TAKEAWAYS The Deep and the Dark web are the hidden part of the internet. When you use it, all the web traffic automatically routes through Tor. If the operating system detects any non-anonymous connection, it blocks it, thus ensuring maximum online protection. Always use a fake name and a temporary email address when you buy something from the dark net shops.
- One of the most common is the exit scam, where a marketplace suddenly disappears and takes everyone’s money with it.
- Fungibility is another key difference between Dash and trackable cryptocurrencies like Bitcoin.
- There are several other browsers you can use, such as Freenet and I2P, but Tor is the most recommended option.
- Its 14,000+ users and 1,000+ vendors leverage multi-crypto flexibility for seamless darknet trading.
- Its affordability and reliability have earned it a loyal customer base.
Onion Search Engine
- The FBI described the takedown as a significant step in disrupting financial cybercrime operations.
- We understand the curiosity to venture into the dark web, but you also need to understand that it’s never safe to venture into this portion of the internet without fully understanding what it entails.
- Many vendors rotate addresses and aliases regularly to avoid tracking and maintain anonymity.
- You’re only scratching the surface when you use the Internet for daily activities—reading news, managing finances, running businesses.
- TorZon Market, launched in September 2022, supports XMR and BTC payments, features established vendors, and offers a user-friendly platform.
The integration of cryptocurrencies like Bitcoin and Monero continues to provide unparalleled anonymity, making these markets a preferred choice for buyers and sellers alike. Abacus Market appeared on the scene in 2021 and quickly became one of the heavyweights among English-speaking markets on the dark web. The categories are well organized, ranging from drugs and fraud to digital products, guides, and malware.What really sets it apart is its focus on security and usability.
Since then, he has dedicated his career to writing extensively about crucial infosec, data privacy, and cybersecurity topics. When he’s not empowering PrivacySavvy’s readers to take control of their online security, Saheed enjoys distance running, playing chess, and exploring the latest open-source software advancements. While this may all sound sophisticated, it is a financial crime and very risky. Those who use these services can still be traced and prosecuted if caught, especially as law enforcement continues to sharpen its tracking tools.
Secure Tor Access
To access the marketplace, dark web users must register first and pass the CAPTCHA test to prove they are human. The site allows users to find and buy a vast variety of products and services. It’s known for its strong security features (like a trusted escrow system, PGP two-factor authentication) and anonymity. In fact, everything is in English, and the site picks up users everywhere in the world.
All Markets At A Glance

To turn it on, just go to the “Settings” and then the “Tools” section of the NordVPN app and activate “Dark Web Monitoring.” In the end, it’s all about staying one step ahead. The more proactive you are, the better you can protect yourself against identity theft and other cyber threats. And, of course, think twice before sharing too much personal details online. Even the smallest details about you can be useful to cybercriminals.
Global law enforcement agencies face mounting challenges in tracking and dismantling dark web operations. In 2025, authorities have increased efforts to identify illicit transactions, monitor suspicious wallet activities, and take down infrastructure supporting criminal trade. However, the rapid evolution of these marketplaces continues to outpace many of these initiatives. Launched in 2023, STYX focuses on financial crime, providing stolen credit card data, hacked bank accounts and access to various cryptocurrency laundering tools. Dark-web marketplaces attract sophisticated cybercriminals adept at launching phishing scams, malware attacks, or ransomware threats. Buyers and sellers frequently face risks from malicious actors posing as legitimate vendors or customers, potentially leading to financial loss or exposure of sensitive personal information.