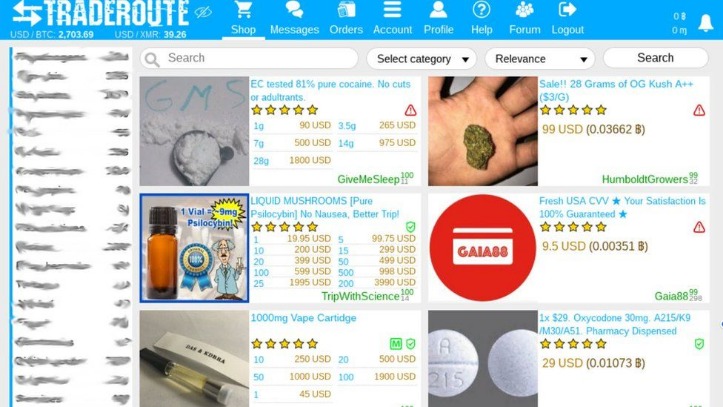
These stolen cards can be used for financial gain through unauthorized charges, account takeover, and identity theft. Card data on the dark web is a valuable commodity, and it’s often sold on specialized marketplaces known as Card Shops. These platforms are hubs for cybercriminals to buy and sell compromised payment card details. Regarding the validity of the stolen payment card dataset, additional details such as user agents, IP addresses, dates of birth, and email addresses suggest with high confidence that the information is authentic and not generated. The validity of cards obtained through phishing can vary; however, they often demonstrate a relatively high validity rate due to several factors.
Risks And Threats On The Dark Web
These sites often look basic or outdated, and their URLs are lengthy strings of random letters and numbers. Keep in mind that visiting the dark web isn’t illegal, but engaging in criminal activity there is. To turn it on, just go to the “Settings” and then the “Tools” section of the NordVPN app and activate “Dark Web Monitoring.” In the end, it’s all about staying one step ahead. The more proactive you are, the better you can protect yourself against identity theft and other cyber threats. Like ransomware, criminals can buy software and inject your devices with viruses. With it, they can spy on people, steal their sensitive data, or secretly control their devices.
Dark Web Prices For Stolen PayPal Accounts Up, Credit Cards Down: Report

One of these, AlphaBay Market, was the most prominent and popular darknet market since the Silk Road. At its height, AlphaBay’s daily sales ranged between $600,000 and $800,000 USD across 300,000 listings for illicit goods, offered by over 40,000 vendors and viewed by some 200,000 users. Because of the range of goods and services found for sale and the conversations that occur around these sales, dark web marketplaces can be precious sources of data on criminal activity. As such, they are normally under intense scrutiny from law enforcement and security professionals alike. Known for its publicity stunt releasing millions of stolen card details for free, BidenCash specializes in credit card fraud and identity theft.
National Public Data Breach (
If you take a quick look through darknet marketplaces, you’ll instantly notice an overwhelming supply of pirated content. We’re talking about even early access to unreleased music, leaked TV episodes, concert footage, and even popular video games before they officially drop. For example, an insider or factory employee might quietly slip away with an unmarked gun and sell it online. Once it lands on a darknet marketplace, it becomes part of the illegal weapons trade.
The price of an account depends on several factors, including the account balance, the bank’s location, and whether the account includes additional information, such as security questions or transaction history. The card’s credit limit, inclusion of the CVV, billing information, and source reliability all impact prices. Regions with stringent fraud detection and advanced cybersecurity measures, such as Germany and the UK, see higher prices due to the increased difficulty of exploiting stolen cards. In contrast, US cards, while more accessible and cheaper, are still valuable due to the ease of fraud. Its intuitive interface and advanced search features make it easy to find local and global products.
Data Leak Checker: Has Your Email Been Hacked?
They are actively promoting the platform on Dark Web hacking-related platforms since late May 2021. The price for cloned cards varies depending on the credit limit, with an average price of $171. The cards were likely compromised online, using phishing, malware, or JavaScript-sniffers, which are increasingly popular among cybercriminals. Stolen card details often end up on the dark web marketplace for a quick profit, and this can happen before you even know about it. Regularly monitoring your credit card statements can help you detect any suspicious activity, such as unauthorized transactions.
Run Antivirus/Anti-Malware Software
From drugs and counterfeit goods to hacking tools and stolen data, this marketplace has carved a niche for itself within the dark web’s underworld. Its popularity among both seasoned criminals and curious novices has raised concerns among security experts, who tirelessly work to combat cybercrime and protect innocent users from falling prey to the dark side of the web. The constant worry for security experts stems from the fact that these dark web marketplaces continue to evolve and adapt, making it difficult to predict their next move. As law enforcement agencies and cybersecurity teams work tirelessly to shut down these platforms, new ones emerge with even greater sophistication. Data breaches like the ones mentioned above highlight the significant threats posed by dark web black markets.
- DarkOwl believes this account may be maintained by DeSnake based on the observation that they leave a similar “Thank You.” at the end of every post.
- You can even find things such as BIN checkers and PayPal cookie converters.
- For this reason, fullz are typically sold by vendors along with ‘logs’, a term for login information and/or web activities history (See Figure 2), and card cloning services (See Figure 3).
- As we mentioned earlier, not everything sold on dark web markets is illegal.
- It features a unique site design unlike any other market yet is still intuitive and easy to use.
Fitzpatrick, in turn, had originally taken over the forum and rebranded it to BreachForums from its original name, RaidForums. BreachForums, an underground forum that has seen multiple iterations and changes in ownership, continues to be one of the most well-regarded English language forums serving cybercriminals across the world – in spite of a rocky year. The forum is frequented by initial access brokers, database vendors, malware developers, spammers, programmers looking to learn new techniques, and everything in between. A dark web search engine like DuckDuckGo offers impressive anonymity features and makes it easy to access the shops. These search engines neither track your search queries nor record any information, improving digital privacy and keeping your data private.
Adopt Secure ATM Habits

Russia’s Criminal Code Articles 228 (narcotics) and 273 (malicious software) allow 15‑ to life‑sentence ranges; in December 2024 a Moscow court gave the alleged founder of the Hydra market life without parole. Belarus requires VPN providers to register with the government, and unregistered use can trigger administrative fines. Kazakhstan criminalizes “distribution of information facilitating drug trafficking,” which prosecutors have applied to forum posts linking to .onion addresses. Adopt a skeptic’s mindset—question every download, every prompt and every request for information—and you’ll shrink the attack surface that criminals and investigators alike rely on to unmask careless users.
🧠 Advanced groups may use PQC to harden ransomware C2s, malware encryption layers, and exfil pipelines. ⚠️ Expect a shift from Tor to multi-protocol darknet ecosystems, with more hybrid models using blockchain-based identity masking. 🎯 Many of these exposures stem from indirect data leaks, such as compromised vendors, SaaS logins, or cloud misconfigurations. Whether you’re defending an enterprise environment or conducting digital forensics, data from the dark web is often the first sign of an incoming breach. Some users claim that mr_white and his team from WHM are to blame for last week’s DDoS while others speculate that HugBunter himself could be mr_white. Interestingly, AlphaBay’s former moderator “Disc0” also chimed in, but using a lowercase “d” this time.
- Plus, there’s a thorough vetting process for new buyers and sellers to keep the community more secure.
- Some vendors offer a “complete package” known as “Fullz”, which includes full personal details as well as financial details like bank account information or social security numbers.
- Freshtools was established in 2019 and offers various stolen credentials, accounts, and host protocols like RDP.
- Just as there are new entrants, the dark web has its veteran markets too, and Brian’s Club is one such market.
The anonymity offered, although not always delivered by dark web networks means the seller has a perception of being relatively safe. The buyer, meanwhile, has to move out of the shadows to profit from their purchases. The risk of getting caught and the considerable legal consequences this brings makes these dark web sites a buyer’s market, hence the low pricing. Sharing a lot of similarities with Exploit, the XSS cybercrime forum also attracts a mixture of threat actors – from simple hacking tool developers to ransomware operators. mark it means it has been verified as a scam service and it should be avoided. Ignoring dark web activity leaves organizations blind to critical signals that often precede full-scale attacks. 🚨 By 2026, companies may be legally required to monitor the dark web for early breach detection in critical sectors.}
Bank Account Access
Dark-web marketplaces often attract attention due to their association with illicit activities; however, these platforms also serve legitimate purposes that align closely with principles of online privacy and freedom of information. Understanding both the lawful and unlawful scenarios helps provide a balanced view of their practical applications in 2025. The threat actor behind the AllWorld Cards marketplace has a clear goal in mind.
Abacus Market appeared on the scene in 2021 and quickly became one of the heavyweights among English-speaking markets on the dark web. The categories are well organized, ranging from drugs and fraud to digital products, guides, and malware.What really sets it apart is its focus on security and usability. It supports PGP encryption, two-factor authentication (2FA), alerts against fake sites (antiphishing), and a verification system for sellers.
Essential Security Tips For Using Dark-Web Marketplaces
Upon his initial arrest, reports suggested he faced up to 20 years for his involvement in the marketplace. When authorities carried out the warrant and arrest in his apartment in Bangkok, his laptop was left unencrypted and the admin account for the market and server logged in. Authorities also simultaneously executed search warrants for the market’s server hardware located in Quebec, Canada. While many cybercriminals are out to simply steal our information, satisfied with creating havoc for individuals or businesses, the majority do it for the money. In today’s digital era, where information is constantly on the move across all digital platforms, an… Blockchain technology is a decentralized digital ledger that records all transactions across a network of computers.