
Once the buyer confirms satisfaction, the funds are released to the seller. The concept of darknets emerged as a response to concerns about digital privacy and government surveillance. One of the most well-known technologies enabling darknets is the Tor network, which was developed by the U.S. Naval Research Laboratory in the mid-1990s and later released to the public.
New Shamos Malware On Mac: Beware Of ClickFix Attacks
Naturally, this makes the dark web a breeding ground for illegal activity. But onion sites can also serve nobler goals, like providing access to information and independent journalism in countries with government censorship. A VPN protects your connection against everyone, not just your ISP and the authorities. It encrypts your connection to prevent outsiders from being able to read your data and masks your IP address with one from a VPN server—so whoever’s looking can’t get any useful information. This process also prevents your ISP from seeing your data or where it’s going.
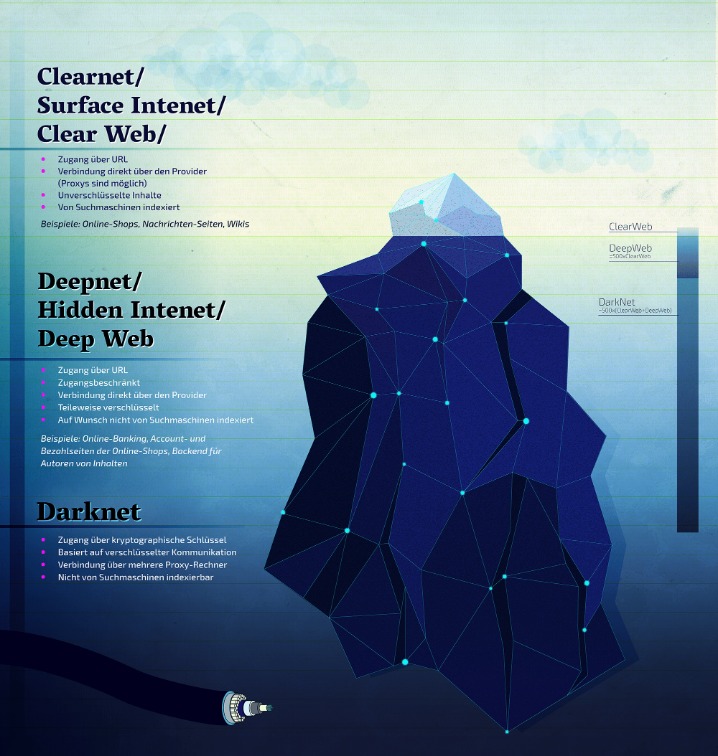
- Deep web content includes anything behind a paywall or requires sign-in credentials.
- The website has a great design and a clean and organized interface that is easy to use.
- Cybercriminals on the dark web marketplace always look for new victims to target them with scams or infect their devices with malware, spyware, or adware.
- N 2025, dark web websites frequently change domains and are often short-lived.
The History Of Darknet Marketplaces
According to a recent trend, the dark marketplaces faced a decline in revenue. Chainanalysis, a blockchain analysis firm, conducted research that shows that the revenue decreased from $3.1 billion (2021) to $2 billion (2024). Once many users begin to rely on the site and store funds in escrow, the operators disappear, taking all the money with them and leaving their customers and clients with nothing. Unfortunately, the dark web hosts not only explicit but also deeply illegal and disturbing content. The markets often share materials related to child exploitation, pornography, and non-consensual recordings, all of which are serious crimes that inflict lasting harm on real-life victims.
What Is Cyber Threat Intelligence?
The significance is in safeguarding the right to free speech and the role of the press as watchdogs. Businesses should be aware of the potential for data leaks and invest in data loss prevention measures. (b) The distribution of the total volume sent across all closed dark marketplaces by migrants (orange line) and non-migrants (blue line). (c) The distribution of the total volume received across all closed dark marketplaces by migrants (orange line) and non-migrants (blue line). Dashed lines represent the median value for migrants (orange line) and non-migrants (blue line). According to court documents and statements made in court, Nesbitt conspired with two other individuals to possess with the intent to distribute, and to distribute, fentanyl and crystal “ice” methamphetamine.
DeepDotWeb Administrators Led Hundreds Of Thousands Of Users To DarkNet Marketplaces
Tor software, in conjunction with the user’s preferred VPN, conceals the user’s location and IP address and is implemented through layers of encryption, akin to the layers of an onion, from which the service derives its name. While some competing darknet softwares are similar to Tor browsers, they typically exist for different purposes. For example, the network dn42 exists to help users form connections and networks rather than to preserve user anonymity.
Law enforcement and security researchers recommend treating all darknet interactions as compromised by default. Cryptomarkets now also operate via messaging apps — harder to index, monitor, or shut down. The affiliate-style cryptocurrency fees were worth around $8.4 million at the time of payment, the DoJ said. If you want more peace of mind, NordVPN has a dark web monitoring tool you can consider using. This handy feature monitors the dark web for signs that your login details or other personal info have been leaked.

Bohemia Market Links
By consistently applying these straightforward security tips, you can significantly mitigate risks and better protect your privacy, finances, and legal standing when interacting with dark-web marketplaces. The Justice Department has shut down a major directory of dark web drug marketplaces and arrested the alleged owners in what federal prosecutors say is a first-of-its-kind operation. The defendants grew and promoted the DDW site, which functioned to drive further traffic to the DDW referral links, generating additional income for the defendants. He registered the domain, made infrastructure payments and maintained control over site content.

Introduction: How Much Of The Internet Can You See?
These markets function similarly to legitimate e-commerce websites, but they are hidden from the typical web, making them part of the internet’s dark side. Cybersecurity companies and researchers monitoring darknet markets face legal and ethical restrictions. Legally, they are limited to observing publicly accessible areas using tools like the Tor browser, without engaging in unauthorized access or illegal transactions. Markets like AlphaBay and Hansa adopted stronger encryption and expanded offerings to include hacking tools and stolen data. However, these platforms often faced law enforcement takedowns, technical issues, or exit scams, where operators vanished with user funds.
Of course, the promise of secrecy and unfiltered access might lure you in, but those same features are what make the environment so risky. Whether you want some pharmaceutical products (drugs) or digital items, you will probably find the products here, and that too at affordable prices. Vice City listens to the problems faced by its customers and vendors and solves them so that they can keep using the platform with ease.

Over the course of the conspiracy, the defendants referred hundreds of thousands of users to Darknet marketplaces. Through the use of the referral links, the defendants received kickbacks worth millions of dollars, generated from the illicit sales conducted on Darknet marketplace accounts created through the site. The darknet is used for anonymous communication, accessing censored information, and protecting privacy.
Dream Market
They were also the first to host a .onion site to make their content accessible to everyone everywhere, regardless of censorship or anti-journalist laws in certain countries. The months and years after Silk Road’s closure were marked by a greatly increased number of shorter-lived markets as well as semi-regular law enforcement takedowns, hacks, scams and voluntary closures. While this topic may seem distant for most people, understanding how these spaces operate is crucial. It helps us stay more vigilant, better protect ourselves, and make informed decisions online.
It is similar to an online store, except it’s not the type you’ll find with a quick Google search. From items like drugs, fake ID cards, and hacked bank accounts to more complex offerings like human trafficking, these sites carry all the illegal activities you can think of. Cryptocurrencies, while offering enhanced privacy, also present significant risks.

And when it comes to paying, the site sticks to Bitcoin (BTC) and Monero (XMR) to keep transactions private. “This is the single most significant law enforcement disruption of the darknet to date,” U.S. Attorney Scott Brady said at a news conference Wednesday in Pittsburgh to announce the charges and the closing of the site DeepDotWeb.



