
Unlike money laundering, terrorist financing is characterized by the fact that funds can be derived from both legitimate and illegitimate sources, such as employment income or student loans. Technologies such as the ones previously mentioned have the potential for mass-adoption due to the low transaction fees and fungible nature of the Lightning Network. Lighting Network solutions can also benefit developed countries by providing secure notification systems, personal messaging, and payment solutions in cases of natural disasters. With a Harpia device, transactions can be initiated and broadcasted to the network, it can run a full Bitcoin and Lightning Network node and connect to Blockstream Satellite6. Many of the solutions currently being developed in Venezuela are largely dependent on the mesh network and focus on being able to provide connectivity despite not being connected to the internet.
Power Your Insights With Data You Can Trust
At the time of writing, the Lightning network has grown to 16,000+ nodes, 69,000+ channels, and total liquidity of 5,000+ BTC. Growth continues as more people worldwide learn how to send and receive fast and convenient micropayments using Lightning network applications. The Lightning network is a second-layer solution for scaling the bitcoin blockchain transaction process. Lightning payments, an integral feature of the Lightning Network, provide an innovative solution to traditional Bitcoin transactions by offering near-instant, low-cost transfers. Built as a layer-2 protocol atop the Bitcoin blockchain, its inception has been a game-changer for the broader crypto community. To address these concerns, the Lightning Network employs a channel-based approach.
- WeTheNorth has a strong community vibe, with an active forum where users interact and share updates.
- Among the most influential supporters was Jack Dorsey, the then-CEO of Twitter, who envisioned a seamless integration of the Lightning Network with Twitter.
- The only information that can be used in this transaction to identify the involved users is linked to the public keys (or commonly called ‘addresses’).
- The Lightning Network has experienced significant advancements recently, aiming to enhance its efficiency and usability as a Bitcoin scalability solution.
- Markets like Nexus and Abacus refine their interfaces yearly, streamlining purchases with features like wishlists and bulk discounts.
User Interface
Despite their controversial nature, these marketplaces continue to evolve, offering a glimpse into the darker side of online commerce. As cyber threat intelligence professionals monitor these markets, they gain insights into emerging threats and malicious activities that can impact organizations and individuals. Whether you want some pharmaceutical products (drugs) or digital items, you will probably find the products here, and that too at affordable prices. Vice City listens to the problems faced by its customers and vendors and solves them so that they can keep using the platform with ease. To access the marketplace, dark web users must register first and pass the CAPTCHA test to prove they are human.
How To Receive Payments On The Lightning Network?
Lightning network fees are likely to be very small compared to the fees charged by miners on the main blockchain. The work done by Lightning network nodes is far easier than that done by miners. Any user trying to charge high fees to allow payments to pass through their node would be avoided. However, fees would soon add up to respectable amounts due to the high volume of Lightning network transactions. Joe and Thad don’t need to set up payment channels with every user on the Lightning network to make transactions with them. Let’s imagine Joe is married to Lou and they have their payment channel for household expenses.
Bitcoin Keeps Dominating Darknet Trade For Fast Deals
One of the biggest problems cybersecurity teams face isn’t a lack of tools — it’s too many alerts. While this topic may seem distant for most people, understanding how these spaces operate is crucial. It helps us stay more vigilant, better protect ourselves, and make informed decisions online.
Top 7 Dark Web Marketplaces
This not only increases transaction speed but also allows for far greater scalability, making Bitcoin more practical for everyday payments. Dark web markets have exploded in scale and reach in 2025, becoming the most dangerous hubs for trading drugs, stolen data, and hacking tools. These anonymous marketplaces—operating mainly on the Tor network—are now a primary threat vector for businesses and cybersecurity professionals.

CISOs Brace For Supply Chain Attacks With Proactive Attack Surface Monitoring
There are app-level privacy upgrades that can be standardized to improve overall privacy on the network. Bitcoin stealth addresses, prominently BIP47, introduced a way to have a stealth, reusable address that only discloses the real address of the user when a notification transaction was made. There are also “fake” CoinJoins who leverage heuristics to confuse on-chain analysis into believing a transaction made by only one person is actually an elaborate CoinJoin.
Using TAILS is yet another security measure that protects your online identity on the dark web. It is a specific Debian-based version of Linux software that leaves no traces of the user activity or the operating system on the computer. It uses the Tor network because it is a popular network that helps to circumvent censorship and online surveillance. Having JavaScript enabled on the dark web can cause havoc because it can reveal your IP address to your website. Also, previously, the Tor browser was vulnerable to JavaScript attacks as it provided hackers a pathway to track your activities by using the session details. Therefore, for security reasons, disable JavaScript on the Tor browser and enjoy an anonymous browsing experience on the dark net.
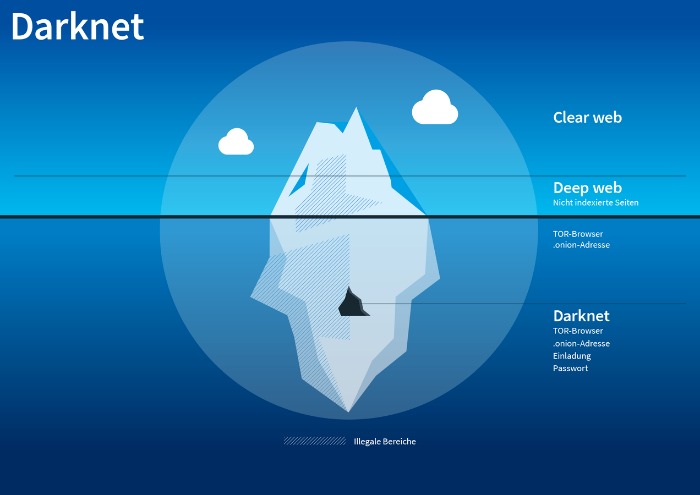
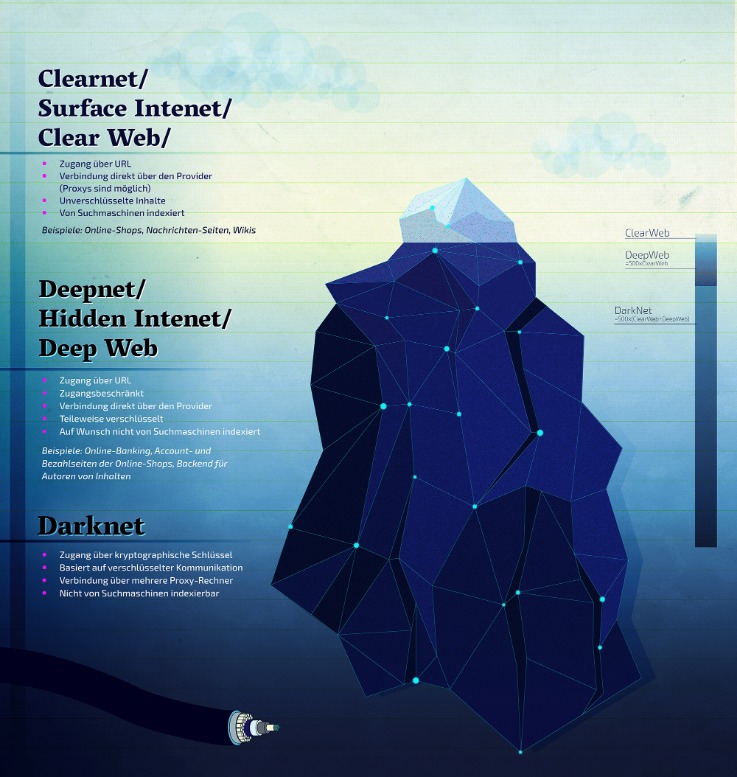
Finding reliable markets is streamlined through updated onion link directories, minimizing phishing risks. Vendor reputations are transparent, with detailed metrics on delivery times and product quality. By 2025, darknet markets have diversified, catering to niche demands while maintaining robust operational security. The Darknet is often utilized for secure communication, discreet information or file sharing, anonymous research without identity exposure, and occasionally for engaging in illicit activities. It is also recognized for hosting underground black markets(darknet markets), whistleblowing platforms, and discussion boards that champion freedom of speech.
Database Migrations
Archetyp Market was dismantled in June 2025 during Operation Deep Sentinel in a coordinated raid across six countries. At the time, it had over 600,000 users, 17,000 listings, and approximately €250 million in transactions. Authorities seized €7.8 million and arrested operators in Germany, Spain, Sweden, Romania, the Netherlands, and the US Europol leads takedown of Archetyp.
Funds are held by the market until the buyer confirms receipt, reducing scams. Automated dispute resolution systems analyze evidence like tracking numbers or product photos, ensuring fair outcomes. Top markets now integrate multi-signature wallets, requiring two of three keys (buyer, seller, market) to release payments, minimizing fraud risks. Darknet markets in 2025 have refined their security protocols, ensuring encrypted transactions remain the standard for safe drug purchases. Platforms like Nexus Market and Abacus Market utilize end-to-end encryption, preventing third-party interception of sensitive data. Buyers and sellers communicate through secure channels, with PGP keys verifying identities and order details.
- Platforms like online freelance marketplaces can use the Lightning Network to facilitate direct, peer-to-peer payments between users with minimal fees and no middlemen.
- Here, you’ll find links to various resources, including educational archives, private forums, anonymous services, and more.
- As of 2020, nearly 57% of the dark web was estimated to contain illegal content, including violence and extremist platforms.
- Simple mistakes—such as inadequate operational security practices, sharing identifiable details, or using compromised devices—can quickly compromise anonymity and expose users’ real-world identities.
- This extra privacy makes it much harder for authorities to track down who runs these markets and where they are located.
Darknet markets in 2025 prioritize anonymity by integrating Tor and Bitcoin as foundational tools. Tor routes traffic through encrypted nodes, masking user IP addresses, while Bitcoin and privacy-focused cryptocurrencies like Monero ensure untraceable transactions. Markets such as Nexus and Abacus automate wallet addresses for each purchase, reducing blockchain analysis risks. Nemesis Market is a relatively new wallet-less shop on dark web where you don’t need to deposit any amount in your wallet before buying products from here.
Even people with little to no knowledge can buy ready-made ransomware and launch attacks on their victims. Unfortunately, the dark web hosts not only explicit but also deeply illegal and disturbing content. The markets often share materials related to child exploitation, pornography, and non-consensual recordings, all of which are serious crimes that inflict lasting harm on real-life victims.



