
Now that you’ve completed the download, it’s time to install the Tor browser on your device. (The installation instructions that follow are for the macOS platform, I’ll mention where it’s different for Windows.) Simply double-click the downloaded file in your download folder. So, once you’ve activated your VPN and your privacy is secured, it’s time to visit Tor’s official download page. It’s impossible to access the dark web with a regular browser like Chrome or Safari.
At the same time, 2024 saw a 42% decline in the number of new darknet marketplaces launched year over year — a signal that while the market is consolidating, it is also becoming more sophisticated. Approximately 300 officers were deployed to secure digital evidence, seize assets, and arrest key suspects. The takedown was led by German authorities, with Europol and Eurojust facilitating intelligence sharing, operational coordination, and legal cooperation across borders. Many people go to the dark web to buy things they can’t find elsewhere, but what if what you’re buying is also trying to harm you? Scammers on darknet markets claim to offer legit tools or services, but instead provide you with malicious software that can infect your device. The market facilitates trades in stolen credit card data, hacked bank accounts, and services to facilitate the laundering of cryptocurrency.
However, always remember that safety should be a top priority, and it is important to weigh the potential risks before venturing into the depths of the Dark Web. Despite taking these precautions, it’s essential to understand that accessing the Dark Web is not without risk. The nature of the Dark Web makes it difficult to trust every website or individual you encounter. It’s important to remain vigilant, exercise caution, and use your best judgment when navigating the Dark Web. The NSO Group’s targeting of app vulnerabilities has also drawn the ire of big tech companies and U.S. lawmakers. In one case, the spyware developer exploited a vulnerability in the popular Meta messaging app, WhatsApp.
Remember, while these Dark Web browsers provide access to the hidden realm, the Dark Web itself can be risky and potentially dangerous. Always exercise caution, follow security best practices, and adhere to legal and ethical guidelines while exploring the Dark Web on your iPhone. Law enforcement agencies across the globe actively monitor the Dark Web to identify and prosecute individuals involved in illegal activities.
Cyber-Attacks And Scams
But onion sites can also serve nobler goals, like providing access to information and independent journalism in countries with government censorship. You can’t access these .onion sites from your normal web browser like the one you’re probably viewing this page on. Before clicking any of the dark web links below, you’ll need to get the Tor Browser (also called the Onion Browser) or another service that provides dark web access, such as the Brave browser.
Is It Safe To Access The Dark Web On IPhone?
No matter what you do online, there’s always at least some risk of being tracked — especially on the dark web. While no method guarantees complete anonymity, you can minimize the chances of being tracked with the right precautions. As a general rule, it’s best to use the default settings in Tor or the Onion Browser. Changing any of the default settings can make websites misbehave or not load correctly.

Seville FfD4 Summit Sparks Global Push For Financial Reform Without US
Hence, it should be the top priority to track these platforms and shut them down as quickly as possible. If you take a quick look through darknet marketplaces, you’ll instantly notice an overwhelming supply of pirated content. We’re talking about even early access to unreleased music, leaked TV episodes, concert footage, and even popular video games before they officially drop. Torzon Market showed up on the dark web in September 2022, and it’s been growing steadily ever since.
onion Dark Web: Exploring The Hidden Depths Of The Internet
It accepts payments through Bitcoin and the Escrow system and ensures that your identity remains anonymous during your purchases. As these marketplaces keep changing, it is critical to stay on top of the main platforms on the dark web worth monitoring. Monitoring dark web markets is crucial, no matter if you are a business or individual, as you can then proactively identify and mitigate potential breaches and cyber threats.
What Are Darknet Markets? Complete Guide
- There’s no denying that the dark web is well-known for illegal activities.
- Explore the underground world of online commerce (Darknet Markets) with our dark web marketplace.
- Make sure that when you download the Tor file, it’s from their official website.
- The Dark Web—a hidden part of the internet accessible only through specialized software like Tor—has become increasingly significant as we enter 2025.
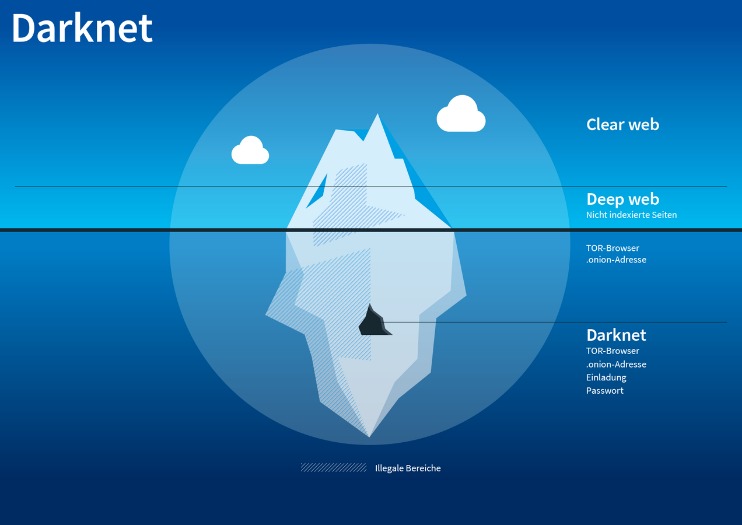
- Although these marketplaces are continuously shut down by law enforcement agencies, they still work today.
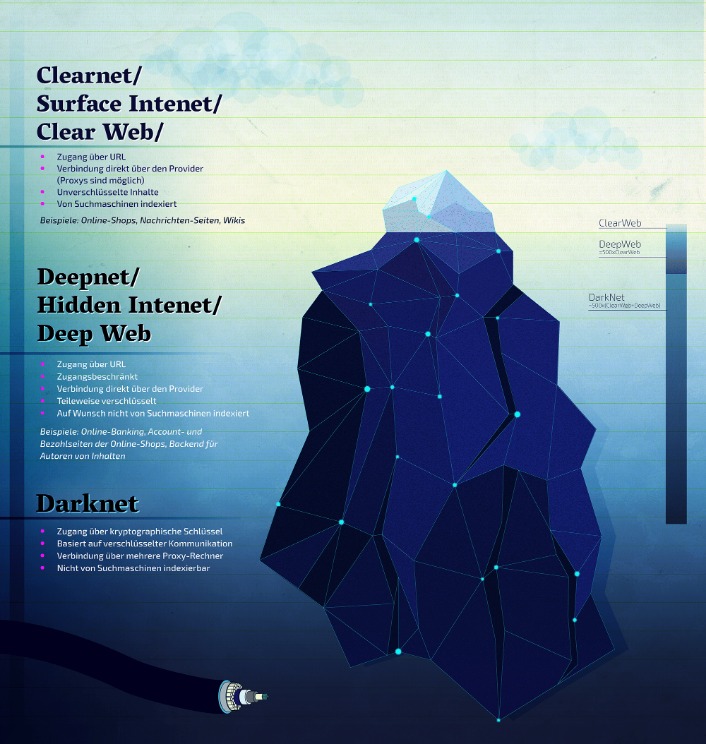
University of Edinburgh student Ian Clarke created Freenet as a thesis project. Freenet was originally intended to provide a way to anonymously interact online, providing ways to communicate, exchange information and files, and to otherwise communicate incognito. For example, the deep web is often a platform used by political activists who own a blog. But it also contains other news and religious sites, private discussion forums, and medical records. You can also find email messages, online bank statements, and much more information on the deep web – information that is usually private and inaccessible by the public on the surface web. The majority of the web is called the “deep web” (often referred to as the “invisible” or “hidden” web).
FAQ – Dark Web Markets 2025 And Cybersecurity
Typical signs of spyware include a slow device, difficulty logging into secure sites, and disabled security software. However, due to its sophistication, Pegasus is much more difficult to detect than other types of malware and often goes totally unnoticed. Ethically, they must minimize harm, responsibly handle any stolen or sensitive data (often notifying victims or law enforcement), avoid entrapment, and maintain research integrity.
Tails always starts with a clean slate and any evidence of the activities you engage in while using Tails disappears when you shut down Tails. This includes evidence of any websites you visit, files you open, passwords you use, and even any other devices or networks you connect to. Tails never writes anything to the computer’s hard drive, running only from the RAM of the computer, which is wiped clean when the computer is shut down. This allows you to use the computer without the risk of corrupting your computer’s normal operating system with viruses or malware. Tails also protects you from possible malware, viruses, or keystroke loggers that may have already infected the computer, as it doesn’t run the operating system already installed on the device.
Darknet Markets – Dark Web Markets Directory Darknet Market Links In 2025

Data gleaned from ransomware and data breaches is available on the dark web. Millions of customers’ personal data, including names, addresses, bank account and credit card account information, and many other forms of sensitive data. Naval Research Laboratory mathematicians and computer scientists in the mid-1990s. The U.S. Army developed “onion routing” to protect intelligence communications online. Later on, the underlying Tor code was released into the wild under a free license, leading to the formation of the Tor Project. In 2008, the first Tor Browser was released, making it easier for any internet users to access the dark web.
Opennet connections are easier to use, but darknet connections provide more security against attackers on the network. I2P can only be used to access hidden sites that are only available on the I2P network. But remember, it’s essential to take all the necessary and important security steps before entering such sites on the dark web. As mentioned before, your ISP and government institutions are not able to see what sites you visit on the Tor network, but they can probably see that you use Tor. Since you’ve now installed the Tor browser, you can safely browse dark web websites and other (previously) hidden websites. Then, simply click the operating system that you are using and download the file.
Here, you’ll find links to various resources, including educational archives, private forums, anonymous services, and more. Dark-web marketplaces attract sophisticated cybercriminals adept at launching phishing scams, malware attacks, or ransomware threats. Buyers and sellers frequently face risks from malicious actors posing as legitimate vendors or customers, potentially leading to financial loss or exposure of sensitive personal information. In general, using the dark web comes with significant risks, including malware, phishing scams, identity theft, and more. While on the Dark Web, exercise caution, stay anonymous by using pseudonyms, and avoid sharing personal details. Be aware of phishing attempts, scams, and misleading websites that populate the Dark Web.
In fact, according to a study that was done in 2020, over 57% of the websites found on the Tor network contained illegal content. A dark web search engine like DuckDuckGo offers impressive anonymity features and makes it easy to access the shops. These search engines neither track your search queries nor record any information, improving digital privacy and keeping your data private.



