The integration of blockchain-based smart contracts is also becoming widespread, automating secure transactions and reducing the likelihood of fraud. Dark-web marketplaces operate through encrypted networks, primarily utilizing anonymity-enhancing technologies such as Tor (The Onion Router) and I2P (Invisible Internet Project). These technologies obscure users’ identities and locations by routing their internet traffic through multiple volunteer-operated servers worldwide, making it extremely difficult to trace activities back to individuals. Tor remains the most prevalent method due to its ease of use and robust anonymity features, but the popularity of I2P is steadily growing due to its increased resistance to surveillance and censorship. JCODE also targets the trafficking of weapons and other illicit goods and services on the internet.
- While this may all sound sophisticated, it is a financial crime and very risky.
- When he’s not empowering PrivacySavvy’s readers to take control of their online security, Saheed enjoys distance running, playing chess, and exploring the latest open-source software advancements.
- Otherwise, here’s how to purchase your first BTC on Localcryptos.com.
- These hackers don’t hide in the shadows as much as you might think.
- Post office staff have no right to open parcels, but when workers find something suspicious, they call the police.
How To Access MarsMarket?
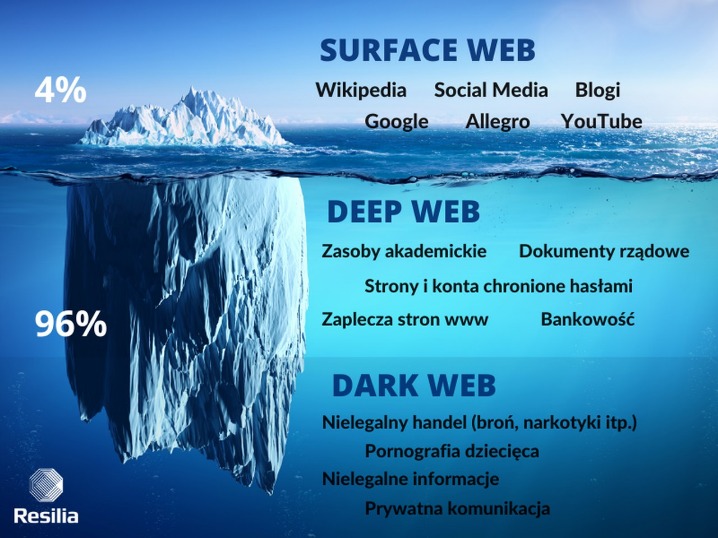
Operating beyond the reach of conventional search engines and law enforcement, this hidden part of the internet thrives on anonymity and encryption, making it a haven to bypass legal constraints. One of the critical issues connected to the dark web is its role in facilitating customs evasion and smuggling operations. Smugglers exploit the dark web to sell contraband across borders, avoiding detection and penalties that would otherwise be enforced through traditional customs channels.

Verified Vendors Only

The suspect had been in the focus of Swedish authorities for some time. He is accused of organizing and coordinating the trade of illegal substances on the darknet via the “Archetyp” platform – particularly in Scandinavia and other parts of Europe. Chainalysis data shows darknet marketplace revenue dropped post-Hydra seizure in 2022 but recovered to $2 billion in Bitcoin inflows during 2024 Darknet market BTC inflow drop and shift to Monero. Abacus alone represented nearly 5 per cent of total DNM revenue, underscoring the ongoing scale of underground commerce. For a local machine configuration, he recommends a computer purchased for cash running Linux, using a local Tor transparent proxy.
Buying Bitcoin (BTC)
One of the most well-known technologies enabling darknets is the Tor network, which was developed by the U.S. Naval Research Laboratory in the mid-1990s and later released to the public. Tor, short for “The Onion Router,” routes internet traffic through a global network of volunteer-operated servers to anonymize a user’s online activity. This technology initially had noble intentions, aiming to protect activists, whistleblowers, and individuals in repressive regimes. However, it soon became a double-edged sword as malicious actors began to exploit its capabilities for illicit purposes.
Other Tools And Links
Simply accessing the dark web and using the Tor browser may already raise government suspicion. This allows you to use the computer without the risk of corrupting your computer’s normal operating system with viruses or malware. Tails also protects you from possible malware, viruses, or keystroke loggers that may have already infected the computer, as it doesn’t run the operating system already installed on the device. In combination with that data, and data gathered by other methods and/or tactics may in fact lead to complete exposure and could eventually lead to the police standing at your doorstep. As I mentioned previously, the dark web is quite popular with journalists, political bloggers and news publishers, and others who run the risk of imprisonment in countries like Iran and others.
Then you have to visit a mail depot to obtain the illegal mail-order drugs. WTN Market is short for WeTheNorth Market, a darknet platform for buying and selling cannabis products with verified vendors in Canada. The WeTheNorth URL is a TOR-based onion address used to securely access the marketplace. WeTheNorth darknet platform uses encryption, escrow, and optional PGP to offer a secure shopping experience for cannabis users in Canada. So we decided to put our money where our mouth is and got working on numerous digital rights projects. We help people fight surveillance and censorship, giving emergency privacy access to freedom fighters and journalists who work in dangerous conditions.
Stay Within Legal Boundaries
The dark web is content that exists on dark nets, which require specialized software (like the Tor Browser), configurations and authorization to access. These can include the previously mentioned illegal offerings, but can also include ultra-private information designed to be shared only with certain parties. Users who wish to gain access to such information are protected by the same anonymity the publishers of the content enjoy.
Top Dark Web Marketplaces Of 2025: A Deeper Dive Into Illicit Trade Markets
Anyone in Canada over the legal age for cannabis use can access our platform. Buyers and sellers must comply with all applicable laws and regulations. Once you have found a vendor you would like to deal with it’s time to do some extra homework on them. For starters, you can put their name into the dread search box, and see if you can find any reviews about them.
Since you’ve now installed the Tor browser, you can safely browse dark web websites and other (previously) hidden websites. Now that you’ve completed the download, it’s time to install the Tor browser on your device. (The installation instructions that follow are for the macOS platform, I’ll mention where it’s different for Windows.) Simply double-click the downloaded file in your download folder.
Later on, the underlying Tor code was released into the wild under a free license, leading to the formation of the Tor Project. In 2008, the first Tor Browser was released, making it easier for any internet users to access the dark web. In 2002 the dark web began to grow significantly when researchers backed by the U.S. The Tor Network provided a way to open safe communication channels for political dissidents, while also offering a channel for American intelligence operatives to communicate from around the globe. Journalists in overly restrictive countries also appreciate the anonymity of the dark web.
New Shamos Malware On Mac: Beware Of ClickFix Attacks
Anyone who’s been burned on an exit scam, or left stranded by a takedown, knows only a few addresses matter. To get started, create your account, and follow the vendor onboarding process. MarsMarket features an transparent vendor rating system, allowing it’s users to review and rate their experiences. Always check a vendor’s ratings, reviews, and policies before making a purchase. MarsMarket is dedicated to providing a safe, private, and efficient shopping experience. Follow these steps to navigate the platform with confidence and enjoy the benefits of anonymous online trade.
The market does not appear to emphasize drugs for purchase in variety and volume as is common with other decentralized markets on the darknet. However, when it comes to darknet markets, the story is very different. Dark web marketplaces are mostly hubs for illicit goods and activities, posing serious risks to users and the wider community.
Plus, there’s a thorough vetting process for new buyers and sellers to keep the community more secure. In a way, it feels more like a private club than an open market, and that’s exactly how the operators want it. Experienced users typically prefer marketplaces with robust vendor rating systems, detailed feedback options, and transparent dispute resolution processes.
Journalists and activists use it to communicate securely in oppressive regimes. You can access it for legitimate purposes like whistleblowing and freedom of expression. However, it’s also used for illegal activities like drug trafficking, weapon sales, and stolen data trading. Law enforcement agencies monitor it for criminal activities, but legitimate users rely on it for privacy protection. In response, cybersecurity professionals, law enforcement agencies, and policymakers around the world are working to combat this growing menace.
This is sometimes convenient when first installing Darknet/YOLO, since the software can be quickly tested without having to train a new neural network. Yes, We The North Marketplace offers low vendor fees, encrypted messaging, PGP support, and a secure environment for Canadian sellers. The official We The North market URL is a hidden service accessible through the TOR network. The WeTheNorth market link is shared on our verified official channels to help users access the marketplace safely and directly. We use advanced encryption and an escrow payment system to protect your privacy and ensure your funds are secure during transactions.



