
It’s important to note that although the dark web has many valuable services, it is also a hangout for cybercriminals. The use of the dark web raises suspicion as it shows there is something you want to do privately. Therefore, the legality of the dark web will mainly depend on how you use it. You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom.

Due to its extensive inventory and reputation for reliability, Brian’s Club has maintained a significant presence on the dark web. Quality and validity of the data it provides justify its higher cost over other marketplaces. The platform’s popularity continues to grow, attracting both new and returning customers. It is a hub for financial cybercrime and offers a wide range of illicit services and stolen data that cater to sophisticated cybercriminals.
You can choose the best darknet (.onion) website that suits you and start surfing. For safer browsing, it is highly recommended to also use a VPN and antivirus software. We’re back with another video in our Webz Insider video series on everything web data. Learn how to automate financial risk reports using AI and news data with this guide for product managers, featuring tools from Webz.io and OpenAI. Freshtools was established in 2019 and offers various stolen credentials, accounts, and host protocols like RDP. It is considered a go-to site for malware purchasing, providing keyloggers, trojans, and other Malware as a Service products.
A Large Number Of Products On The Ares Market
It is considered very secure thanks to strict user validations and transparent payment and vendor review procedures. Russian Market has consistently remained one of the most popular and valuable data stores on the dark web. Its affordability and reliability have earned it a loyal customer base. The platform’s activity has increased significantly over the past year, indicating its growing influence and market share in the underground economy.

The market started in 2021 in Canada and features both international and Canadian users. The market offers things like malware, fake documents, and financial fraud services. This market is not open to the general public and is subject to a thorough vetting process to ensure its security.
Cyber threat intelligence (CTI) helps organizations predict, understand, and defend against cyber threats, enabling proactive protection and reducing the impact of attacks. Payments were not made in euros or dollars, but with the anonymous cryptocurrency Monero, which is particularly difficult to trace. Designed for the elite darknet operator seeking streamlined access, surgical control and unmatched discretion. The seller does not make clear how they are obtaining these cards, but threat actors are known to clone cards, or access banking information from stole credentials, particularly through Stealer Logs. Get the latest in privacy news, tips, tricks, and security guides to level-up your digital security. If you only want to mask your IP address and don’t need to access the dark web, then going online with a VPN is much easier and faster than using Tor.

In short, red rooms appear to be more of a modern-day urban legend than a verified reality, blending horror fiction with the fears of the digital age. One of the largest community-driven hidden services directory in Tor. The oldest .onion links directory which is actively maintained up to date. The most important thing is to ensure that you never click on links that you’re not sure of their source. Also, it should be common knowledge not to share personal information online.
Subscribe To Our Blog For More News And Updates!
- However, this feature is only available on iOS, Android, and Windows.
- While these marketplaces continue to serve legitimate purposes, such as enabling secure communication and privacy protection, they also remain hotspots for illicit activities and cybercrime.
- The focus of the investigators was on a 30-year-old German who is suspected of having acted as the administrator of Archetyp Market.
- Hence, if you participate in them, whether knowingly or unknowingly, you can end up putting criminal charges on yourself, and in some extreme cases, even imprisonment.
- This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacyRadar.com page.
The only way to access the dark web is by using the correct browser and knowing the URLs of the pages you want to visit. Scroll on to learn more about dark web links (also called Tor links or onion sites), get the right links for some of the best Tor sites, and find out how to visit them safely. Understanding both the lawful and unlawful scenarios helps provide a balanced view of their practical applications in 2025.
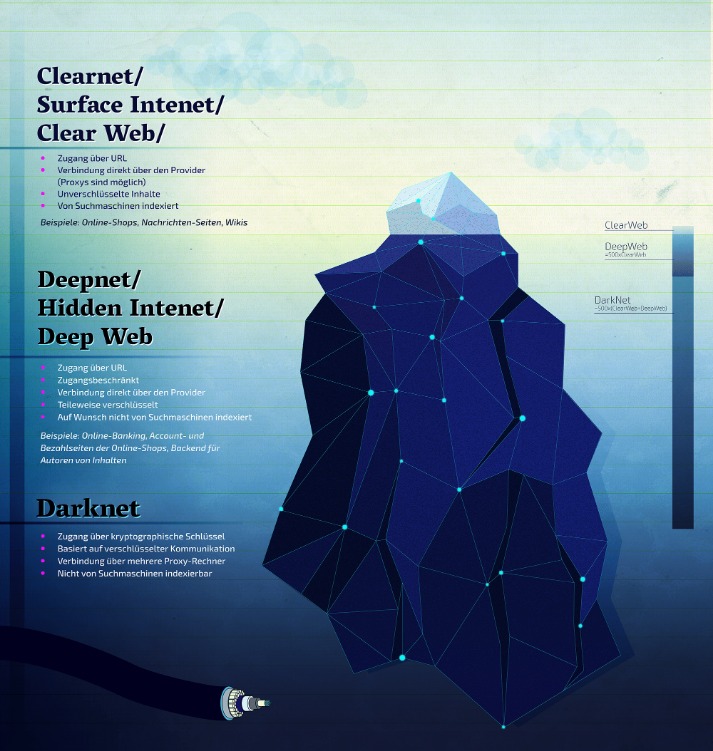
Understanding The Deep Web, Dark Web, And Darknet (2025 Guide)
Stopping their growth takes serious effort from US agencies like the FBI, often working hand-in-hand with international law enforcement. The fallout for victims whose data is stolen and sold can be devastating. They suffer losses such as identity theft, financial loss, and emotional distress due to damage to their personal and professional lives. They really don’t care about the loss and dilemma of the victims whose data has been stolen. These hackers don’t hide in the shadows as much as you might think.
Top 10 Dark Web Markets
Swiss based e-mail service, encrypts e-mails locally on your browser. Radar Rundown The dark web consists of many websites with uncensored information; choose a suitable … There are several other browsers you can use, such as Freenet and I2P, but Tor is the most recommended option. In this era, it takes one wrong click and all your sensitive data ends up in the wrong hands. Therefore, you need to take your privacy seriously and start by using strong and unique passwords for every online account you open. According to the United Nations Office on Drugs and Crime (UNODC), all guns are manufactured legally.
Torzon Darknet Market

As listed above in our article, even respected organizations like the BBC and ProPublica have a version of their site on the dark web. There are often copious amounts of how-to articles, software exploits, and hacked credentials for sale. Not every visitor is a criminal, but this is where most cybercrimes begin. Onion links have no regular domain names registered under the domain name registry. Instead, they are designed using a cryptographic key and can be accessed only through software like the Tor browser. Keep in mind that you’ve to use very specific keywords when searching.
Top Darknet Markets 2025
While this may all sound sophisticated, it is a financial crime and very risky. Those who use these services can still be traced and prosecuted if caught, especially as law enforcement continues to sharpen its tracking tools. Unfortunately, the dark web hosts not only explicit but also deeply illegal and disturbing content. The markets often share materials related to child exploitation, pornography, and non-consensual recordings, all of which are serious crimes that inflict lasting harm on real-life victims. Such content fuels a dangerous cycle of abuse, violence, and exploitation.
These software are also capable of launching DDoS attacks and phishing campaigns. Too-good-to-be-true investment offers are another classic scam on the dark web. Early participants may see some profit, but that money usually comes from new victims, not actual earnings. Eventually, the system collapses, and most people lose their entire investment. So, if a “business opportunity” sounds too perfect, it probably is.
Scams And Fraudulent Activities On The Darknet Markets
Through the dark web, users in places of high censorship can also access information and news. TorLinks serves as a backup or secondary directory site to the popular Hidden Wiki. It’s divided into commercial links (from crypto services to gambling sites) and non-commercial links (like social media).
Darknets are not limited to criminal activities; nation-state actors use these hidden platforms for espionage, disseminating propaganda, and recruiting agents. The significance lies in the potential compromise of national security. Governments and businesses must invest in advanced threat intelligence, cyber defense, and counter-espionage measures. Although some of these markets prohibit certain extreme content such as violence or exploitation, most operate with very few rules beyond ensuring the security and anonymity of their users.



